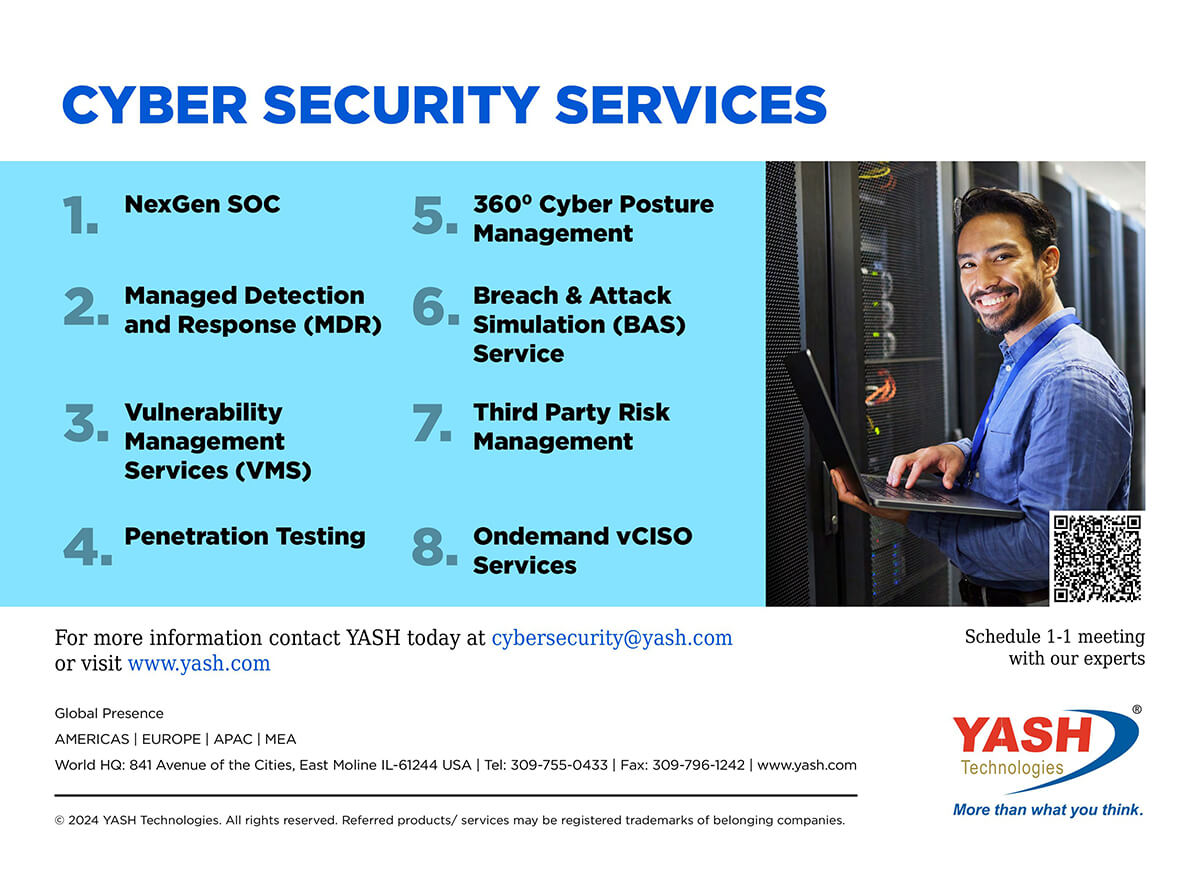
Cyber Security Services.
How YASH Manged Security Services Create Business Impact and Deliver Value.





YASH Differentiators.
- Cyber security solutions that improves business outcomes and enable swift and precise response to cyber threats
- Access to the Digital Collective™, which combines:
- Design-led digital innovation with human experience
- Customizable digital platforms
- Collaborative ecosystem of first-class technology partners and innovators
- Cyberscecurity strategy & risk-compliance-architecture advisory
- Active Defence framework: Reduces alert fatigue by 95% and focus on true positive alerts
- Build alert rules from the scratch using ADF
- Achieve compliance by default as per industry standards (NIST, ISO, PCI-DSS, HIPAA)
Frequently Asked Questions (FAQs).
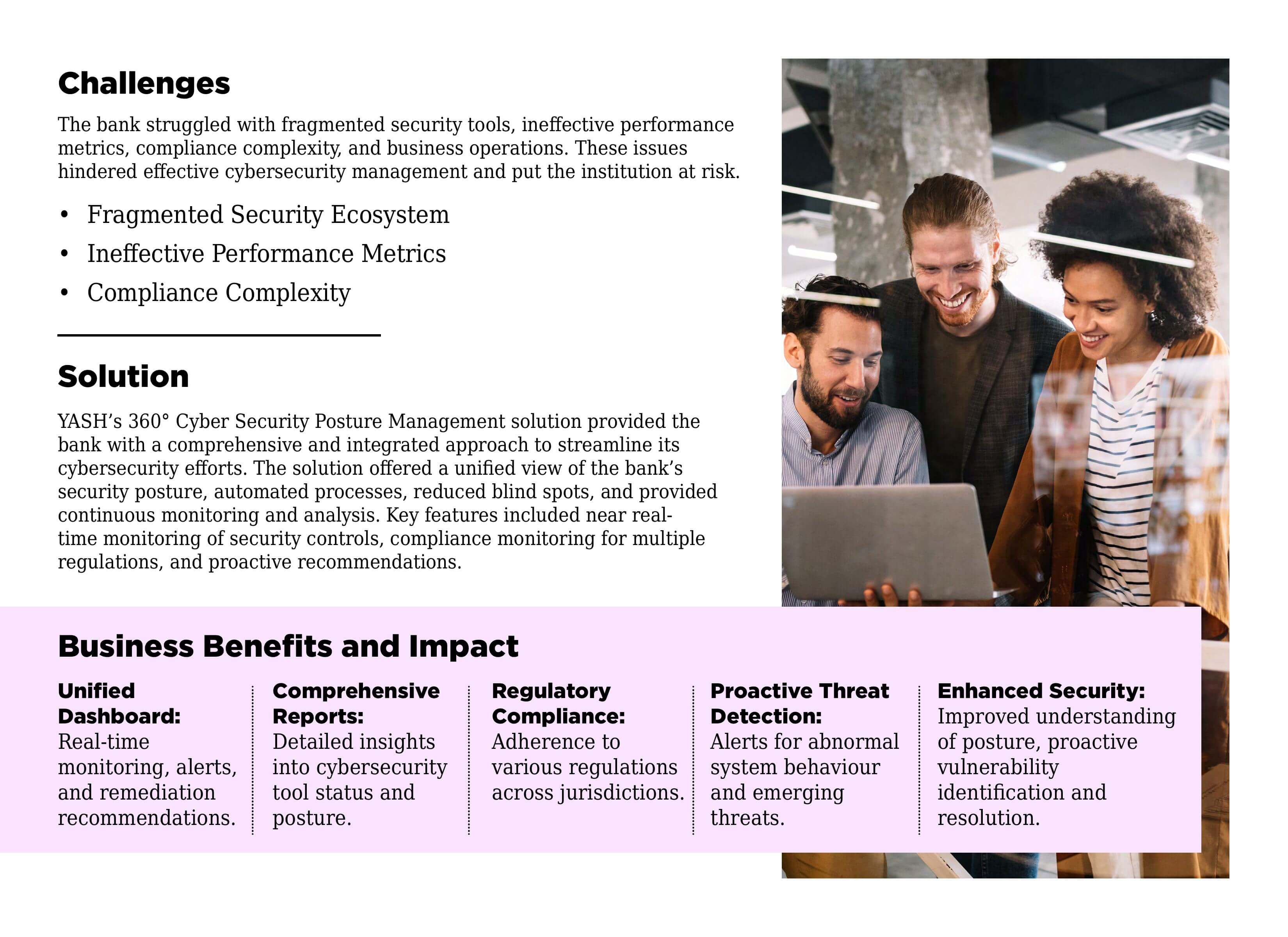
We offer managed cybersecurity services and solutions tailored to your needs. Our services include AI-augmented SOC, Cloud Security, Vulnerability Management Services, Penetration Testing Services, Third-Party Risk Management, and more.
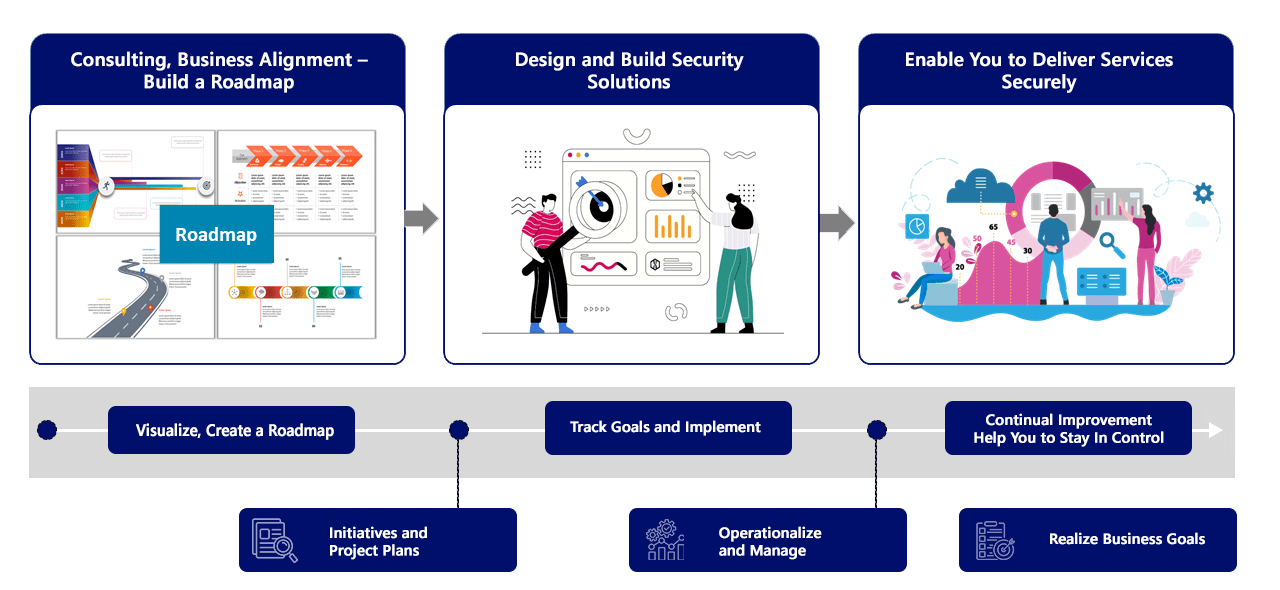
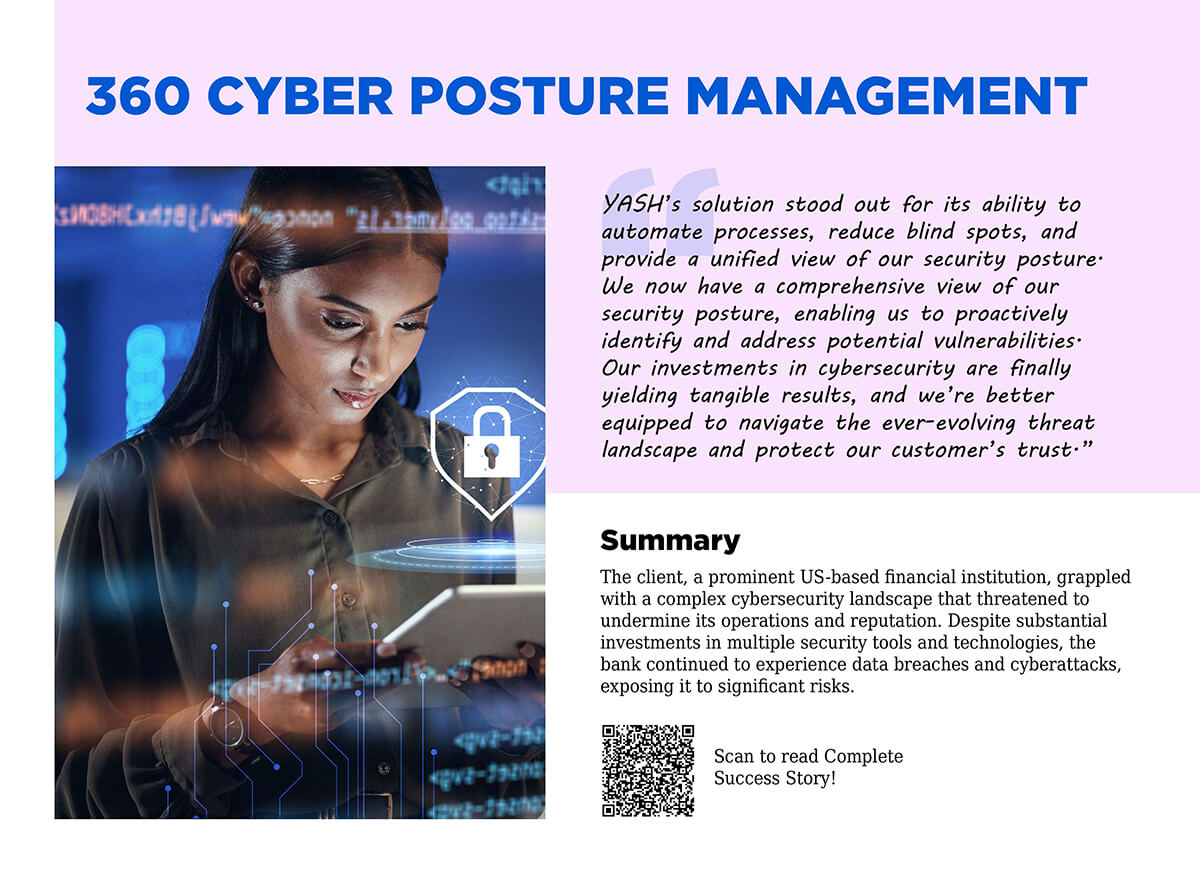
YASH cybersecurity services help you to elevate your cybersecurity posture, identify gaps, and develop a roadmap to enhance your security maturity. We help you navigate the complexities of the cyber landscape, enabling secure business growth while minimizing disruptions.
Just write to us at cybersecurity@yash.com or click here to contact us. Our experts will contact you for a nonbinding consultation and get you started.
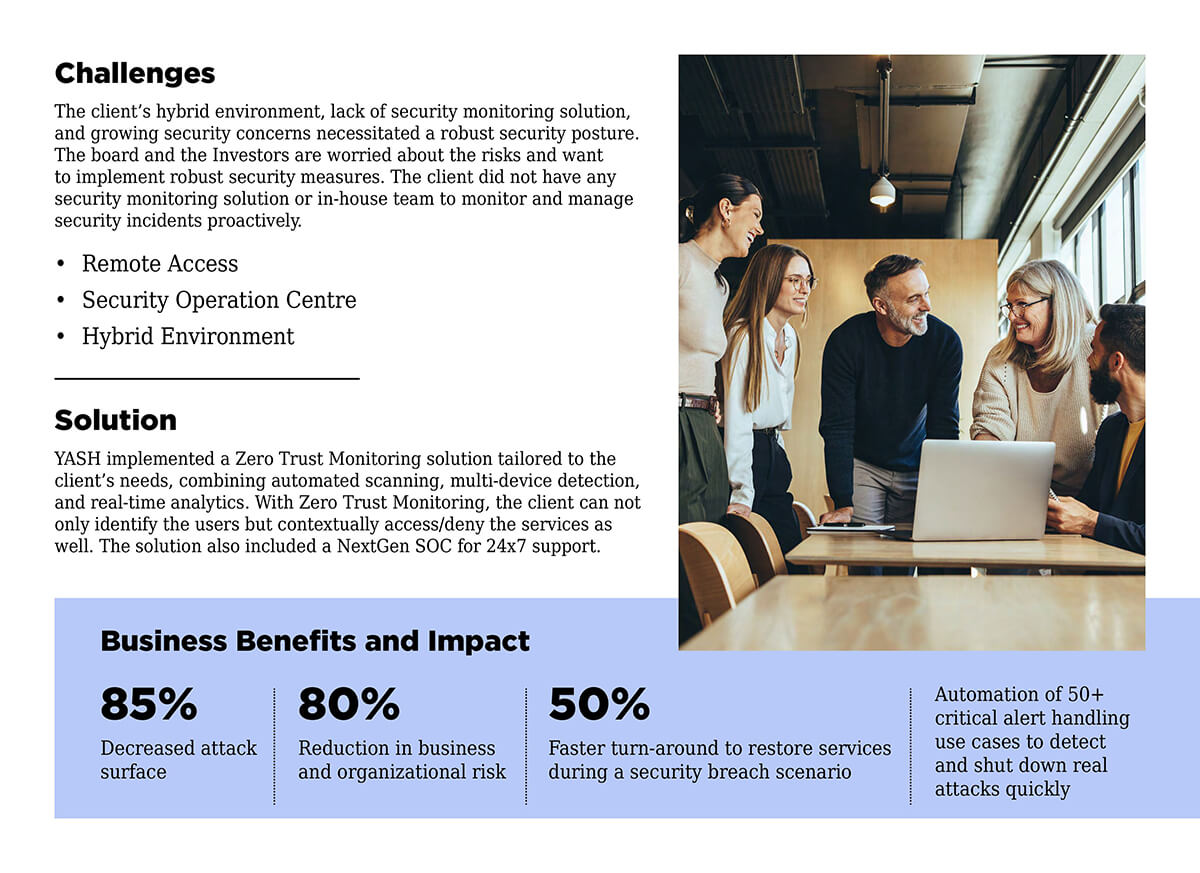
Yes, we can be a 24/7 Security Partner by helping you with L1/L2 Monitoring, SIEM Engineering, and Incident Management.
Yes, we have been helping businesses comply with leading industry standards like HIPPA, NIST 2.0, SOC II, GDPR, DORA, etc.