Secure your Cyber-Physical Systems with the YASH OT Security Services
Publish Date: July 1, 2022Attackers are moving away from IT and using the OT to penetrate.
In simpler times, there was no intersection between information technology (IT) and operational technology (OT). It ensured that business processes and systems were immune to risks that have become all too common. While the IT-OT convergence now allows organizations to set new operational standards and achieve greater cost efficiency, it has also increased susceptibility to cyber threats. The difficulty today is the exposure of OT leading to security risks and impact to productivity impacts. The ease of accessibility to sensitive data makes OT networks an easier target for hackers, and an attack for organizations today means a loss of revenue and reputation.
“Gartner predicts that by 2025, cyber attackers will have weaponized operational technology (OT) environments to successfully harm or kill humans leading to a financial impact of over $50 billion. Hence security and risk management leaders should also be concerned about real-world hazards to humans and the operational environment along with information theft.”
According to researchers at FireEye, criminals are increasingly shifting the target to OT networks worldwide. As a result, vital industries and critical infrastructures like traffic systems, energy, mining, and water management are at risk of catastrophic attacks.
The rise of OT network breaches has been a high-priority trend for cyber security experts. These attacks, which can occur without warning, are more indiscriminate and dangerous. The increased sophistication of the attackers, whether IT or OT, necessitates a change in thinking to address cybersecurity.
Do we move the needle, and in which direction?
Technology adoption in healthcare, oil and energy, fintech, and telecom industries continuously faces the challenge of securing their networks. These organizations are often unaware of the blind spots that their attackers lurk in. Complexity also multiplies when combined with legacy systems in OT. Recent cyberattacks have led some nations to consider state-sponsored hacking a significant threat to cybersecurity. Launched in May 2022, the attack on Greenland’s healthcare network provided a stark reminder of the potential impact these attacks can have on nations. A recent report warns that OT networks are unprepared for cyber-attacks and, therefore, vulnerable to cyber espionage and state-sponsored attacks within and outside the power generation sector. It says the increased interconnectivity between critical infrastructure and IoT devices creates a ‘blind spot’ that can be exploited by state-sponsored action or by highly sophisticated lone-wolf hackers. The list goes on.
How can YASH help
We at YASH have evolved an approach that will move the needle in the right direction. Adopting a hybrid system – a combination of automated and manual detection- is the hour’s need.
- Conduct discovery exercises more often than before.
- Scanning the OT networking systems for technical pitfalls and conducting assessments for potential risks can drastically reduce potential losses.
- Performing test cases for hardware, firmware, and network API is essential as it allows for seamless application onboarding.
- Finally, a risk-based approach under which the vulnerabilities are validated and fixed, procedures are reviewed, and development reports are generated is required.
- Evaluating the success of OT systems under this approach requires rigorous testing and monitoring.
- Build a rapid response to deal with any future events through table top exercises
Secure yourself for tomorrow, today
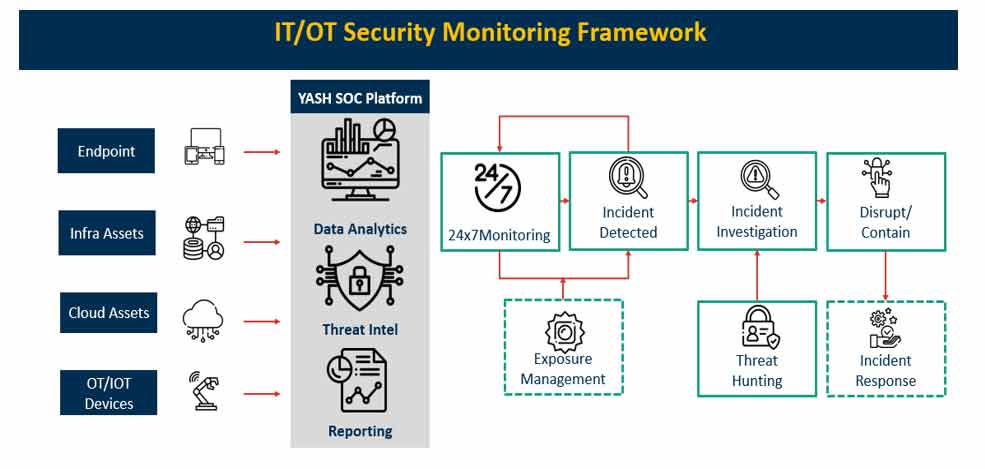
At YASH Technologies, we believe monitoring and fine-tuning the security policies must build a strong defence. We do:
- Device Security Monitoring (DSM) brings these objectives together, thus keeping an organization ahead of threats.
- Apply and Evaluate use cases related to your environment, and conduct essential testing of security controls through the Device Security Testing Suite (DSTS).
It helps organizations to identify, quantify, and prioritize cyber security risks and vulnerabilities for all devices.
We help define an integrated security plan, implement DSTS and DSM optimally, ensure a fast and easy solution that delivers 100% visibility into industrial networks, and aligns with overall enterprise security. Some of the critical functionalities of DSTS and DSM are:
- Device Firmware Analysis: Firmware reverse engineering and modification, mostly hardcoded for sensitive data.
- Web/Mobile Application API Penetration Testing: ASPT simulated cyberattacks against your computer system to check for exploitable vulnerabilities.
- Radio Protocol Security: Conduct protocol, traffic, and BT / BLE / Zigbee / 6LoWpan analysis.
- OT / IoT / IT Asset Discovery: Near-instantaneous visibility into managed and unmanaged assets for effective industrial cybersecurity.
- M&A Due Diligence: M&A due diligence, if applicable, on target companies’ industrial networks to rapidly fulfill M&A requirements.
Making a difference with YASH Technologies
Working with us enables you to implement the above principle into existing systems without requiring network changes. Our flexible cloud and on-premise deployment options make the solution suitable for connected or air-gapped networks. We work towards solving industry challenges of complex infrastructure, lack of secure development, and the massive population of IoT devices. With a holistic approach enabled through our Cybersecurity Technical Advisory, we achieve the aspired standards of a secure hybrid IT-OT environment.
If that’s what you’re looking for, join the growing network of clients that have received remarkable business results at scale with the advisory, support, and technical services we offer!
Click here to know more about YASH’s OT security services
Senthilvel Kumar
Vice President – Cyber Security Services
Senthil is a cyber security Practice Head and VP at YASH offering advisory on cyber security solutions to CxO's, CISO, Board Level Executives for building a robust security modernization programme covering on-prem and Cloud.