Patch It or Pay the Price: Uncovering Your Vulnerability Score and How to Sharpen Your Defenses
Publish Date: March 12, 2024Imagine your IT infrastructure as a castle wall. Cracks and loose stones represent vulnerabilities – weak points that attackers can exploit to breach your defenses. Vulnerability management is your team of vigilant guards constantly scanning the walls, identifying these weak spots, and patching them before attackers can strike. These vulnerabilities can stem from various sources, like poorly configured firewalls or outdated software, and can open your systems to malware infiltration, unauthorized access, and other threats. By proactively addressing these weaknesses, you can significantly reduce your risk of a cyberattack and keep your valuable data safe.

Enhancing Vulnerability Management Scores
Bolstering vulnerability management involves a comprehensive vulnerability assessment to scrutinize, categorize, and prioritize weaknesses within network infrastructures, computer setups, and applications. These assessments are instrumental in pinpointing potential threats and rely on automated testing tools. Key types of vulnerability scans encompass:
- Network-based Scans: Designed to uncover potential network security breaches and identify vulnerable systems across wired or wireless networks.
- Host-based Scans: Delve into servers, workstations, and network hosts, providing detailed insights into configurations and patch histories to uncover vulnerabilities.
- Application Scans: Focus on testing websites, software, and applications to identify vulnerabilities and address improper configurations.
- Database Scans: Target weaknesses within databases to preemptively thwart malicious attacks such as SQL injection vulnerabilities.
For organizations to minimize their vulnerabilities and get good scores on vulnerability assessments, following certain best practices is imperative. These include:
- Maintaining comprehensive records of all network-connected devices
- Proactively deploying verified patches for systems and software to fortify against recognized vulnerabilities
- Educating employees to identify and thwart malicious emails, links, websites, and endpoint threats capable of breaching networks or individual computers
- Maximizing automation in vulnerability management processes and employing a unified approach for accessing pertinent data, reports, and KPIs
Foundations of Effective Vulnerability Management
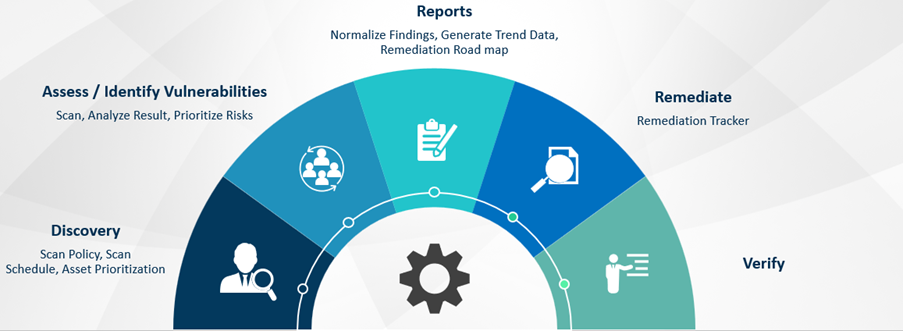
At the core of a vulnerability management program is typically a vulnerability scanner that automatically evaluates and comprehends threats across an entire IT landscape, generating lucid reports that help businesses prioritize the vulnerabilities they must remediate or mitigate. The critical steps of the program are:
- Identifying Vulnerabilities: Any vulnerability management process begins with detecting the security loopholes across various accessible systems. This includes scrutinizing desktops, laptops, servers, databases, routers, firewalls, switches, and printers. The process involves checking for open ports and active services on these systems, logging in where permissible, and gathering pertinent details. Subsequently, the acquired information is correlated with known vulnerabilities to assess potential risks.
- Evaluating Identified Weaknesses: Once the vulnerabilities have been identified, they must be assessed to understand their risks for an organization’s cyber risk management strategy. Various scores and risk ratings aid in prioritizing vulnerabilities for resolution, with the Common Vulnerability Scoring System (CVSS) often serving as a prevalent reference. However, enterprises must acknowledge that vulnerability scanners might occasionally produce false positives. Hence, incorporating additional considerations alongside risk scores becomes crucial at this stage of the assessment process.
- Resolving Vulnerabilities: After prioritizing the vulnerabilities identified, the treatment typically proceeds through:
- Remediation: The preferred course of action involves fully resolving a vulnerability wherever possible, eliminating exploitability.
- Mitigation: In cases where complete remediation isn’t viable, efforts focus on minimizing the vulnerability’s susceptibility to exploitation.
- Acceptance: Organizations may leave low-risk vulnerabilities unaddressed if fixing them is too expensive compared to the potential harm they could cause.
After addressing all critical vulnerabilities, conducting a follow-up scan is advisable to validate the efficacy of the implemented actions and ensure the infrastructure remains free from further threats.
Vulnerability Reporting: Enhancing Risk Management
Constant improvement in speed and accuracy of detecting and remediating vulnerabilities is critical to managing the risk they represent – this is why leading organizations continually evaluate the efficiency of their vulnerability management program and maintain reports of their actions. With the right insights, IT teams can choose the remediation techniques that help them fix new vulnerabilities with minimum effort. Security teams can use the reports to track vulnerability trends and inform the leadership on risk reduction progress.
The ROI Metrics for Vulnerability Management Systems (VMS) Programs
The actual value of a VMS program is the sum of all the breaches that didn’t occur due to the timely detection of vulnerabilities. Analysts recommend the following metrics to gauge the success of a VMS program:
- Mean time to address/mitigate most harmful vulnerabilities for critical assets
- Mean time to identify risky vulnerabilities
- The average window of exposure
- Number of security incidents caused by vulnerabilities that were exploited
Due to unrealistic and siloed approaches, most organizations fail to reduce their exposure to threats while self-assessing risks. They must, therefore, rethink their approach to the VMS program by partnering with specialists who can ensure maximum security with minimal resources.
Distinguishing MPS-led VMS Programs from MSSP-managed VMS Programs
A Managed Security Provider (MSP) is an external entity remotely overseeing a business’s IT infrastructure, aiming to fortify network vulnerabilities without compromising overall operational efficiency. These providers conduct assessments of an organization’s current system and craft tailored solutions to bolster security.
In comparison, Managed Security Service Providers (MSSPs) offer more comprehensive security measures, ensuring the accessibility and usability of all facets of a company’s information systems by its employees and customers. MSSPs prioritize security to a greater extent, delivering holistic IT solutions. They leverage advanced tools to identify vulnerabilities, mitigate threats, and optimize network and asset safety. With extensive expertise in risk scanning, MSSPs can identify vulnerabilities within the attack surface, adjacent to it, or within proximity. MSSP solutions excel in preempting both the immediate and enduring impacts of cyber-attacks.
How YASH VMS Offering Benefits Customers
YASH goes beyond simply scanning for vulnerabilities. We leverage the industry-standard OSSTM methodology for a thorough technical assessment of all connected systems within your network. Our goal is to identify weaknesses and provide actionable solutions that help you remediate them and lower risks to manageable levels.
We understand vulnerability management is an ongoing process, not a one-time event. We don’t stop at the scan report. We track every vulnerability until it’s resolved, ensuring corrective actions are taken and preventing recurrences. This ensures your security posture remains strong and adapts to evolving threats.
To learn more about our VMS program, visit https://www.yash.com/services/cyber-security-services/risk-based-vulnerability-management/
Senthilvel Kumar
Vice President – Cyber Security Services
Senthil is a cyber security Practice Head and VP at YASH offering advisory on cyber security solutions to CxO's, CISO, Board Level Executives for building a robust security modernization programme covering on-prem and Cloud.
















