Proactive Security in a Digital Era: Managed Detection and Response (MDR) and Beyond
Publish Date: February 9, 2024Cybersecurity threats are becoming more aggressive in intensity and success rates as organizations rapidly embrace digital transformation and shift to cloud-based platforms. While many enterprises are trying to catch up by deploying new cybersecurity measures, safeguarding IT infrastructure, enterprise applications, and networks is only getting costlier and more complex. Undoubtedly, evaluating the host of available tools, handling a surge in vendor relationships, maintaining data privacy, and securing scarce cybersecurity talent have become daunting tasks for nearly all organizations.
The Managed Detection and Response (MDR) services address such problems, helping companies rapidly identify, investigate, and respond to suspicious activities and threats that can sabotage business operations. It combines the skills and experience of thousands of risk advisory specialists and proven processes and technologies to improve the overall cybersecurity structure.
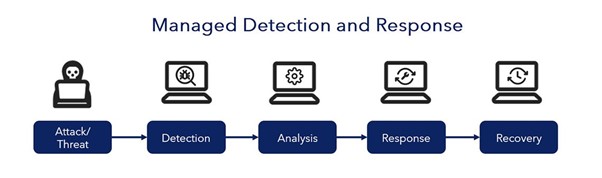
How does MDR work?
The MDR approach, delivered remotely using pre-defined technologies, allows businesses to collect relevant logs, data, and telemetry inputs from an organization’s operational environment. The information is then analyzed comprehensively using threat intelligence, automation, and individual expertise to provide constant monitoring, high-fidelity threat detection, and containment. Additionally, proactive threat-hunting services are provided to search for emerging threats and multi-stage attacks before they happen.
The key benefits of MDR:
- 24/7 monitoring by a team of seasoned experts proficient in endpoint threat detection, incident response, forensic investigation, and specialized support
- Swift response, remediation, and containment based on intelligence derived from a diverse and extensive customer base
- Reduced alert fatigue and decreased security capital expenditure, leading to an increased return on investment
- Improved compliance adherence and reporting capabilities
- Heightened resilience against attacks, fostering a fortified environment with a robust security posture
Difference between MSSP and MDR
Organizations commonly enlist managed security service providers (MSSPs) to oversee their firewalls and security infrastructure. While MDR solution providers and MSSPs share some similarities, they diverge significantly in technology usage, expertise levels, and the scope of services. MSSPs primarily concentrate on alerting, security monitoring, and administration, often leaving response actions to the client. They handle passive tasks, heavily relying on automation, and typically engage with customers through a portal interface.
Conversely, MDR encompasses proactive real-time threat hunting by a team of human experts, maintaining continuous system monitoring. MDR delivers alerts, triages indicators of compromise (IoC), and consistently executes responses to threats, investigating and remediating them to safeguard the infrastructure supporting business operations and data security. Through MDR services, organizations leverage analysts’ expertise by employing advanced security tools and staying updated with real-time global databases, which is crucial in keeping pace with evolving adversarial tactics and techniques.
Partnering with an MDR service provider offers a valuable alternative to constantly pursuing the latest advanced security products. It involves integrating Endpoint Detection and Response (EDR) tools, which are generally complex for security operations teams to comprehend and manage effectively.
Selecting the Right MDR Service Partner
When evaluating potential MDR service partners, it’s crucial to consider their ability to align with diverse industry needs and evolving customer demands. A proficient MDR service provider should possess the following capabilities:
- Data Integration and Analysis: Proficiency in correlating and analyzing signals and telemetry data from various sources is essential for robust analytics, threat detection, forensic analysis, and responsive actions.
- Device Management Solutions: A comprehensive approach encompassing managed and unmanaged devices is vital. Leveraging systems like user and entity behavior analytics, network traffic analysis, endpoint detection and response (EDR), and endpoint protection platforms (EPP) ensures thorough coverage.
- Swift Transition from Detection to Response: The ability to pivot swiftly from detecting threats to initiating incident response is critical to mitigate potential risks effectively.
- Continuous, Efficient Coverage: Offering uninterrupted, round-the-clock coverage with low mean time to detect (MTTD) and mean time to respond (MTTR) is imperative to address emerging threats swiftly.
Moreover, a competent MDR service should cater to companies embracing multi-cloud strategies while supporting critical on-premises workloads. Their expertise should extend to proven processes designed for operational technology (OT) and Internet of Things (IoT) systems, ensuring comprehensive security solutions across various environments.
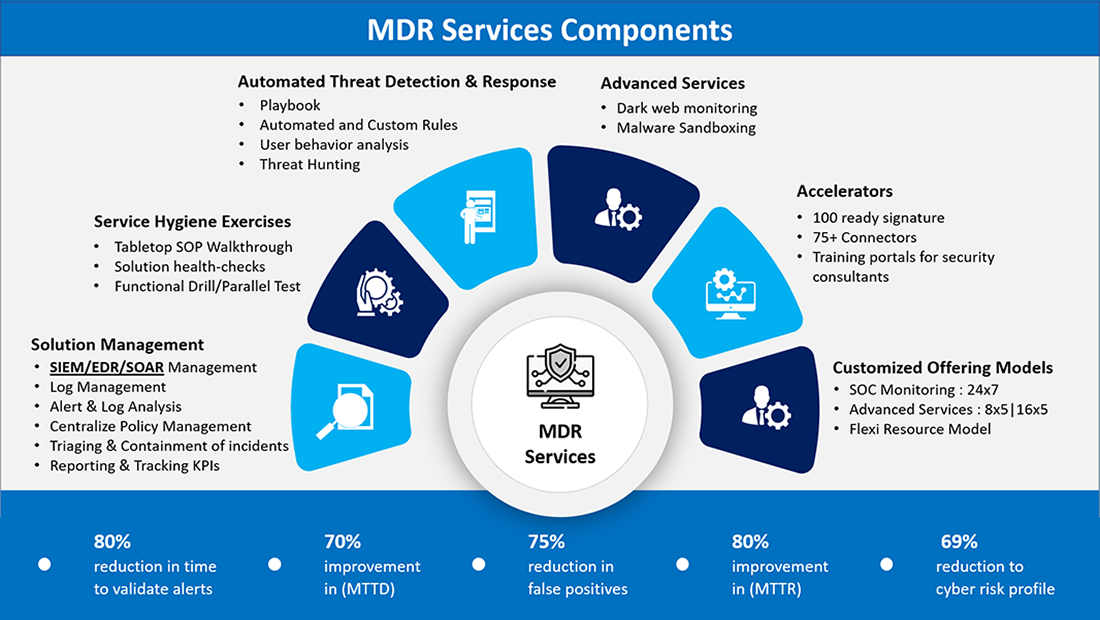
MDR Services by YASH Technologies
YASH Technologies is one of the primary security partners, enabling clients to fortify their business transformations amidst an evolving threat landscape. Our bespoke Managed Detection and Response (MDR) services provide holistic protection, including continuous security monitoring, threat hunting, contextualized threat intelligence, and a comprehensive incident detection-analysis-response system.
YASH MDR Services
Our detection and response solution merges various data sources, employing Security Information and Event Management (SIEM), logging, and analytics for end-to-end threat identification. YASH integrates Attack Surface Management (ASM) and robust vulnerability processes, ensuring ongoing monitoring and proactive management of potential attack points within internal and external assets. This proactive approach preemptively identifies and addresses security weaknesses, deterring possible exploitation by adversaries.
Our MDR services, which utilize broad intelligence networks, safeguard against internal and external breaches, eliminating vulnerable data repositories and securing revenue-generating resources. We reduce attack surfaces and expedite response times to minimize downtime costs. By integrating premier cybersecurity tools and our processes, we streamline security efforts for optimal outcomes and reduced complexity.
YASH doesn’t solely strengthen security; we enhance operational efficiency and cost-effectiveness by enabling swift scalability and centralized security measures across diverse locations. Moreover, we facilitate compliance with location-specific regulations, offering real-time threat evaluations and comprehensive enterprise visibility to support informed decision-making for business leaders.
Explore our MDR services and success stories at https://www.yash.com/cmp/22/cyber-security-servicesmanaged-detection-and-response-services.html.
Senthilvel Kumar
Vice President – Cyber Security Services
Senthil is a cyber security Practice Head and VP at YASH offering advisory on cyber security solutions to CxO's, CISO, Board Level Executives for building a robust security modernization programme covering on-prem and Cloud.
Shivendra Sharma
Technical Architect - Cybersecurity
Shivendra is a cybersecurity solution architect at YASH, focusing on building security strategies and executing solutions for security leaders that connect with their business objectives.
















