Zero Trust Monitoring – A Necessity Amidst the Dynamic Cyber Environment
Publish Date: July 1, 2022IT Security is no longer a security team’s responsibility alone. It is now everyone’s business to contribute and build robust security for the organization. IT systems/services are multi-tenant and cannot be merely controlled by access control, particularly if they need to scale to partners and the supply chain. Today, every business unit – production, sales, marketing, customer relationship, partners/suppliers, HR, finance, and accounting is technology reliant. You can’t afford to assume your internal communications and underlying systems are secure. Variations and deviations from the expected system/user behavior are inevitable. Every organization requires a focus and an agile security model to adapt to the business demands/changes.
This includes protecting access to business applications, data, users, and all the underlying devices — across the entire enterprise — against threats (both inside and outside of your corporate boundaries). And you can only do this by building trust by verifying your enterprise infrastructure at every level, from user identity and access management down to network traffic. Here’s where Zero Trust comes in.
Why is Zero Trust Monitoring Relevant Amidst Evolving Cyber Attacks?
Zero trust is based on the assertion that no user and their access to applications/services/data should be trusted by default. Zero trust involves least-privileged access. It establishes context-based trust where it considers user identity, location, endpoint security posture, etc., with stringent policy checks across every access step.
Companies Need Zero Trust Monitoring, NOW!
A recent Forrester study reported that 82% of organizations, both small and large affirm their commitment to adopting a Zero Trust security architecture.
Gartner predicts that, 30% of enterprises worldwide will adopt Zero Trust Network Access (ZTNA) by 2024 as a top Cybersecurity initiative.
But why now more than ever and why Zero Trust?
Enterprises need a comprehensive security approach built for the new reality of cyberattacks. With the growing trend of remote work, many people connect remotely from unauthorized endpoints or not enterprise-managed endpoints such as the home computers that are outside of an IT department’s control. Such employees’ home environments are more vulnerable, and organizations risk being struck by data breaches. Data breaches and increased global regulations have made network protection difficult, so enterprises are turning to next-generation security solutions.
With its fundamental principle, zero trust monitoring treats every app access, user, and device with suspicion and involves thorough and continuous checks. It also addresses cybersecurity internally through least privileged access and establishing trust but verify model after thoroughly assessing elements within a cyber environment, as mentioned earlier.
Organizations Without Zero Trust Monitoring are at a Risk
Companies without a zero-trust monitoring system in place are at various risks, including,
- Susceptibility to easy targets
- Increased vulnerability to attacks due to assumed user or application trust
- Weaker cybersecurity compliance
- Increased number of potential failure points
- Reduced likelihood of business continuity in case of large-scale cyberattacks
- Data exposed to bad actors or malicious apps or programs
- Increased possibility of a ransomware attack
- The increased amount of anomalous behavior that goes undetected or unrealized
What Current OEMs are not Addressing?
OEMs have always been at the forefront of network security, but the threat landscape is ever-changing significantly in recent years. As a result, OEMs must take advantage of every opportunity to increase their visibility into the network, understand how it is being used and prioritize any gaps in their controls.
OEMs produce products with unique traceability requirements, and they also may have more extensive distribution networks, often disconnected, and fewer cybersecurity resources than their brand counterparts. OEMs and suppliers to the manufacturing industry are also cyberattack targets, so it’s critical that they monitor their data center networks, train and test recovery procedures, and take advantage of development resources to help address ongoing threats.
Additionally, OEMs are responsible for ensuring that they have secured all customer data in their possession and control. It would include monitoring data stored on devices connected to the network and any protocols or applications that transfer information from one device to another.
With Zero Trust Monitoring, OEMs can monitor their external exposure and detect possible threats before they affect their customers’ data
How Zero Trust Monitoring Helps Strengthen Your Cyber Security Environment?
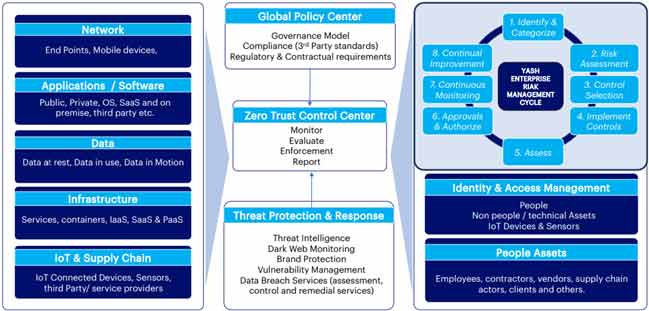
Zero trust monitoring service or approach covers every aspect of your cyber environment. It provides a remarkably efficient strategic architecture that helps minimize risk and create agility. So, here’s what zero trust monitoring covers.
- Network: Endpoints and mobile devices
- Applications/Software: Private, public, SaaS, OS, on-premises, and third-party
- Data: Privacy obligations, Data in use, motion, and at rest
- Infrastructure: Containers, IaaS, PaaS, SaaS, and services
- Devices: IoT-connected devices, sensors, third-party, etc.
- People Assets: Contractors, employees, vendors, clients, etc.
- IAM: People, technical assets, non-people, IoT devices, and sensors
What does YASH have to Offer?
At YASH, we help enterprises build a robust security model that delivers “Trust but verify.” We offer a comprehensive Zero Trust Monitoring package, Zero Trust Monitoring – NexGen SOC services that include 24/7 event monitoring, efficient event handling, detailed security analysis, and synchronized management of devices, applications, and hybrid systems. The combined impact of all these services is enhanced cybersecurity and improved compliance.
Benefits of Zero Trust Monitoring
Benefits of Zero Trust Monitoring services include:
- Quicker incident detection & support
- An accurate and responsive incident management
- Increased service availability through a co-shore engagement model
- High-quality incident management
- Cloud-based SIEM tool for increased scalability reduced deployment time and realized quicker ROI
- Apply threat hunting principles to detect previously undetected threats
- Reduced false positives through analytics and threat intelligence
- AI-based threat investigation
- Cloud-Scale data collection for all the devices
- Rapid incident response with KPI/SLA-driven integrated threat management delivery and automation of various everyday tasks
Click here to know more about YASH’s Zero Trust Monitoring – NexGen SOC.
Ref:
https://www.gartner.com/en/articles/the-top-8-cybersecurity-predictions-for-2021-2022
https://diginomica.com/could-zero-trust-security-have-prevented-massive-solarwinds-attack
Senthilvel Kumar
Vice President – Cyber Security Services
Senthil is a cyber security Practice Head and VP at YASH offering advisory on cyber security solutions to CxO's, CISO, Board Level Executives for building a robust security modernization programme covering on-prem and Cloud.















