Importance of carrying out Security Tabletop Exercises
Publish Date: August 16, 2018Context:
It is always good to be agile, vigilant and ready with your organization’s cyber incident response plan by running the exercises for evaluation. These exercises, commonly named “Tabletop exercises” aka ‘TTX,’ enable organizations to identify and investigate probable emergency situations in an informal environment.
These exercises initiate discussions among the teams while examining the rolled out operational plans and help propose improvements.
Uncertainty gives rise to fear of security threats and attacks. Thus, Tabletop exercises hold key potential for an effective preparation to handle a cyber incident.
Need to Know:
The Security Tabletop Exercise (TTX) involves a diverse group of Organization’s professionals in an informal setting, discussing simulated situations/events. This type of exercise is intended to stimulate discussion on various issues relating to a hypothetical situation.
- It is leveraged to assess plans, policies, and procedures or to evaluate types of systems needed to guide the prevention of, response to, and recovery from a defined security event.
- Security Tabletops facilitate understanding of concepts, identifying strengths and shortfalls, and/or achieving a change in attitude.
- Participants encouraged to discuss issues in depth and mature decisions through slow-paced problem solving compared to quick and spontaneous decision making that occur under actual or simulated emergency conditions.

- Tabletop simulations provide a great roadmap for organizational awareness and training for inevitable security incidents.
- They allow a team to come together in a low-stress environment and assess their procedures and plans. Typically, with the most organization, these exercises are conducted once a year as a compliance requirement or for internal requirements.
- So how do we better design and deliver a simulation that drives our security program toward a state of continuous improvement?
What is it all about?
A tabletop exercise (TTX) is an exercise which is held in an informal setting intended to generate discussions of various issues regarding a hypothetical, simulated emergency incident.
TTX evaluates the already known tools, processes, and expertise to identify the uncertainty and unknowns and possible risks your organization may need to respond to. Exercises involve a roundtable of experts, competent consultants, and technical staff. They use scenario-based real-world experiences in the organizational environment to provide views, risks, concerns, and critical feedback on the business strategies and technical risks. Such exercises provide an opportunity for planning, preparation, and coordination of resources during any kind of attack.
TTX is leveraged to
- Enhance general awareness
- Validate plans and procedures
- Assess the types of systems needed to guide prevention of, protection from, response to, and recovery from a defined incident.
Goals
The goal of a tabletop exercise is not just to create a comprehensive and full proof cyber incident response plan. Instead, it should be a planning activity where you discuss and identify deficiencies, along with corresponding corrective actions, which leads to a comprehensive plan.
The most common goals we see in practice today are:
- To achieve compliance with regulation, policy, or standard
- To validate the effectiveness of cyber incident response plans
- To evaluate the need for external cyber support resources
- To enhance cyber awareness and readiness
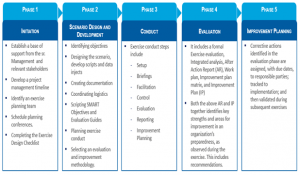
Approach
The approach to Security tabletop exercise is aligned and evolved around the current state controls organizations have in place, and this enables to effectively measure their incident responses relative to their environment.
- Use-Cases are defined based on various threats as applicable to Customer’s environment.
The approach includes but not limited to the following:
- Documentation review including incident response plan, crisis communications procedures, IT policies, and network topologies.
- Comprehensive assessment of organization’s security program including deep dive analysis of incident response including the current state maturity of IR plan, adherence to IR plan, IR coordination, internal and external communications, and technical analysis.
Testing with Tabletop Exercise
Change is inevitable, and like any policy, process, protocol, or procedure document in the organization, the incident response plan also requires constant updates due to the changes in your environment over the time. Your organization continuously mature and grow and so is your security program. Validation, update, practice, and testing your plan on a regular basis using different exercises are, therefore, must to ensure its effectiveness and robustness.
- A tabletop exercise is intended to test the planned incident response but it can be used for a variety of audiences ranging from policies, decision-making and compliance with business continuity processes and technical process flows.
- The process involves conducting an exercise on paper (task-based), to test the IR plan followed by simulation of attack in the environment.
- A penetration testing with the help of red team assessment method can be used. The complexity of simulation depends on the expected results. The attack can take place between a team of trusted internal or third-party attackers mimicking a live attack on your network and a team of trusted network defenders.
- The attacking team usually follows pre-agreed targets or methodology.
- The defending team includes incident responders, forensic and malware analysts. Simulation efforts can be then followed by actual physical environment attacks to test the plan in a real-life scenario.
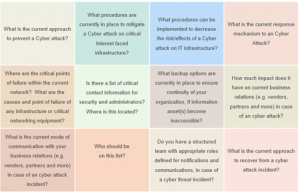
Security Tabletop exercises provide answers to…
Best practices for using security tabletop exercises
- Make your preparations right
– The objectives, scope, and participants must be determined during the planning phase. - Enforce boundaries and remain focused
– Provide guidance by a facilitator to prevent deviations. Focus on the productive conversations for detection, containment, eradication and recovery from an incident. - Summarize the story
– A summary of post-attack activities done in the past to be reviewed with lessons learned documented to suggest improvements. - Involve multiple teams and domain expertise from the organization
– Prepare a list of experts, consultants, facilitators, and expertise across functions suitable for table exercises to formulate a team of security guardians. - Coordinate
– A tabletop exercise tests the incident response capability as well as provides the opportunity to coordinate across various teams. Security preparations are not isolated efforts but a comprehensive action. - Expand the vision
– A tabletop exercise provides a view of unharmed environment so that plans to mitigate the attacks can be seen with a plain canvas. Visionaries can provide answers to seal the gaps in the process and can help with their decision-making ability. - Get everyone on the train
– Security attacks are not only a concern of and limited to action by security planners and executioners. Each stakeholder in the organization is equally responsible and should be capable of understanding the incident response plan and should help execute it if required. - Execute dummy attacks
– Similar to mock fire drills, cyber-attacks as simple as desktop issues or server authorization compromise can produce a significant awareness about the possible risks and business disruption associated with the attacks. - Communicate a clear scope of the exercise
– Getting value from the exercise depends on its conduct and the acceptance of the objective across the team. Participants need to understand that the exercise is conducted to make the organization more prepared with the future action plan and therefore a concoction of expertise, vision, forecasting, and risk identification along with meticulous planning and protocol administration is required. - Remove communication barriers
– Ensure participants understand when and how to communicate their views, concerns, and decisions to ensure healthy communication and information exchange. - Involve experts from the fraternity
– In case your organization needs third-party support, industrial organizations can provide services to help companies conduct tabletop exercises. Also, it is good to invite outside agencies like government or legal for a mutually beneficial partnership. - Keep attention for secondary benefits
– Tabletop exercises are good opportunities to validate existing processes and procedures. It can help find knowledge and implementation gaps related to the organization’s understanding of security and improve the security awareness. - Make the exercises realistic
– Tabletop exercises are to visualize future attacks and get prepared with eh solutions. Instead of imaginary examples, the exercise should deal with real-life experiences and scenarios.
Reaching towards complete confidence
The question that all organizations want to answer as Yes is “Are you ready for an incident?”. An organization needs to be completely confident about its response planning including the procedures useful to protect from a possible cyber-attack or to remove or nullify the implications. We have discussed how the tabletop exercise can be useful to build this confidence. In a nutshell, the exercise identifies the audience, defines scope, sets methodology, defines a scenario, executes the exercise, and publishes the results to advise the improvements in the response planning. Tabletop exercises are not the answer to all the incident planning related problems, but it helps to have them to make decisions about security planning, protocols to address incidents and to create a risk-free environment.
Get more than what you think from your security solutions with YASH.
Manga Sridhar Akella-Program Manager Information Security @YASH Technologies