Securing IoT Networks: How to Enable Effective Security Testing and Deployment
Publish Date: July 27, 2023By 2023, it is estimated that over 30 billion IoT devices will be deployed worldwide, increasing the attack surface and potential vulnerabilities. Security has become a significant concern for various industries and market segments as IoT expands. With IoT, it’s possible to remotely track and control connected factories, vehicles, healthcare equipment, and other linked devices. Unfortunately, data breaches can have disastrous consequences for both manufacturers and consumers.
There must be more than user authentication and data encryption measures to secure IoT networks effectively. It’s crucial to ensure that all assets involved in the network have been developed securely throughout every phase of their software development lifecycle (SDLC). Security requirements should inform the architectural design, deployment, and testing processes.
Why is security testing a challenge?
Ensuring security through testing is a complex issue in IoT because it requires addressing the interconnectivity between devices and the interaction between multiple technologies in the setup. It goes beyond functional requirements, including validating user access through enforced classes of privileges, preventing hardware-software modifications, and safeguarding data from unauthorized access through USBs, Wi-Fi, Bluetooth, and other wireless technologies. Entities testing an IoT system must consider these factors to ensure comprehensive security testing.
IoT security standards
Awareness of laws and industry regulations is crucial to start on the right foot with IoT network security. Standards such as IEC 62443 provide procedures for software development in industrial communication networks to mitigate risks, while ISO 27001 offers a framework for implementing an information security management system (ISMS). An ISMS enables the management of security practices, monitoring of threats, enforcement of encryption, and handling of incident management. Adherence to such standards helps ensure a more secure IoT network.
Security testing for SDLC
Organizations building IoT devices are often familiar with IEC 61508 and its safety software lifecycle, which shares similarities with IEC 62443-4-1’s Secure Product Development Lifecycle Requirements. When security and safety teams collaborate for testing, they must document all safety requirements in application lifecycle management (ALM) tools and allocate defined security requirements to different technical domains.
It’s crucial to break down system security mandates and trace them back to high-level requirements to avoid security gaps in the design. The process lifecycles between safety and security overlap and are displayed in a V-model process lifecycle.
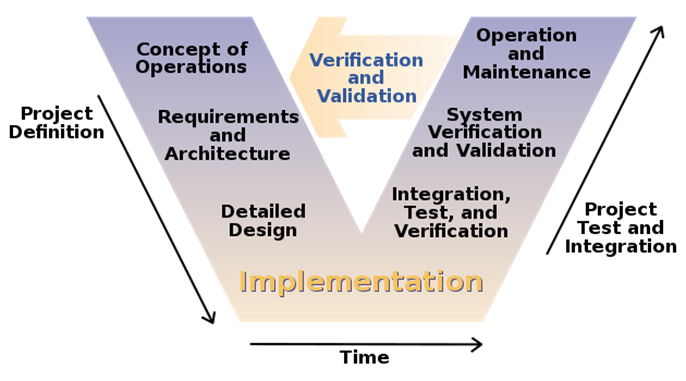
Image Source: Wikipedia
Creating system-level test cases is crucial to meeting security requirements, and these cases are defined with precise input and output criteria. Quality analysts (QAs) must understand the levels of abstraction in security requirements and testing and realize each test case with its associated security requirements. Dynamic application security testing (DAST) includes various methods such as penetration testing, API testing, service virtualization, functional security testing, fuzz testing, UI testing, and test case code coverage.
Moving to the left side of the V-model, system-level security requirements are decomposed and integrated into the high-level architectural design. Test cases here assess interactions between components, subsystems, and functional capabilities using service virtualization, API testing, fuzz testing, and security functional testing.
At the detailed design level, teams construct functional code units to support security while ensuring the requirements link back to parent requirements and unit-level test cases built by the security system engineer. The software engineer can also link the code that deploys the requirement to the requirement artifact, offering traceability in an ever-evolving set of requirements. This traceability proves valuable if a requirement is eliminated or planned for a future release. The direct traceability to the exact code that deploys the need makes removing the code with minimal negative impacts easy.
The software engineer must create multiple unit test cases to validate requirements and functional capabilities and ensure the code supports different threat scenarios.
Security deployment happens at the bottom of the V-model. During security deployment in IoT, engineers commonly use C and C++ to code as per requirements. However, these languages have coding constructs that can result in security issues, such as buffer overflows where hackers can inject malicious code into memory. A solution to these problems is to use security coding analysis at the core level of development.
Static application security testing (SAST) is an effective tool for testing system vulnerabilities and should ideally be the first level of testing. Tools such as Parasoft C/C++test integrate well with IDE and can be incorporated into DevOps pipelines to introduce security into the organization’s build process. Companies using Scrum and DevOps CI/CD methodologies have reported advantages such as superior code quality, lower testing costs, and faster speed-to-market.
As they step back into the software development lifecycle, security teams can understand all the levels where security measures must be applied. When they look at the bigger picture of IoT, testing must address its connectivity with enormous scope, taking care of the context for connected devices. Such testing can be a combination of SAST and DAST.
Securing IoT devices with YASH
At YASH Technologies, we know that security assurance for IoT applications and APIs must be embedded continually into all SDLC stages. We help our customers properly configure the application components that build their IoT environment. We also integrate security testing tools into development and QA cycles for on-the-go and, wherever possible, automated assessments.
With YASH’s accepted test standards, frameworks, and APIs, you can counter the most recent vulnerabilities and threats for all the IoT devices, applications, and APIs exposed to production.
We are here to embed security into your IoT development cycle, fix existing issues, and prevent new ones. To book a consultation, write to us at info@yash.com