Enhancing Security in Mergers and Acquisitions (M&A) with Identity and Access Management (IAM)
Publish Date: September 6, 2023According to S&P Global Year, 2021 witnessed an unprecedented surge in the speed of mergers and acquisitions (S&P Global Market Intelligence revealed that by the second quarter of 2021, the value of M&A activities had crossed the remarkable $1 trillion mark). This surge gained momentum in the new age economy, such as “Digital in Every Walk Of Life.”
Furthermore, Refinitiv Data’s report added staggering numbers to the picture. In 2022, the total value of pending and completed deals skyrocketed to an astonishing $3.6 trillion.
However, the true impact of this frenetic M&A activity becomes palpable after the dust settles and the newly merged or acquired companies attempt to extract maximum value from their new structures, navigating through the intricacies of doing business in the post-mergers.
In this landscape of transformation, early strategic decisions become essential. Finding the equilibrium between operational efficiency and security is vital to sustaining the business as usual, particularly integrating multiple distinctly operating system environments. Similarly, Another important aspect of M&A is access management. As organizations seek to harmonize and optimize their combined resources, striking this balance ensures a foundation that propels growth while safeguarding critical assets.
During these intricate processes of M&A, the importance of a robust Identity and Access Management (IAM) framework cannot be overstated. Business dynamics shift when parent companies and acquired entities come together, highlighting the necessity for effective IAM to seamlessly deliver goods and services to their customers. Managing identity and access risks across multiple business applications is very intimidating at this phase. One entity wouldn’t want to risk another business service because of the unknowns in the IAM space.
Challenges of M&A and IAM’s Role: M&A scenarios become more complex due to varying systems and user types. This makes IAM pivotal to operating business systems and streamlined user provisioning and managing privileges. Additionally, IAM is a crucial defense mechanism against the rising tide of cyber threats because it safeguards sensitive data and intellectual property by implementing stringent authentication and authorization measures, fostering a unified security posture and seamless collaboration.

Derisking Access Risks at the Beginning:
A good starting point could be to ask the experts to evaluate the risks during the pre and post-integration stages to eliminate any risk of business disruptions. Organizations with strong cyber postures get their CISOs early in the cycle to plan and design the target IAM required to minimize disruptions. The best strategy is to avoid business disruptions due to the merger of two identity repositories into a single enterprise. It can be achieved by establishing a baseline identity framework that ensures that individuals have the right access levels at the right time, preserving data integrity.
How The Systems Will Have To Be Configured And Delivered To The World
- Merging IAM systems of two different organizations can be technically complex. Integration may require careful configuration and business process alignment inspections of various IAM components, such as user identity repositories, authentication mechanisms, access policies, provisioning workflow systems, etc. Incompatibilities or conflicts between systems could result in poor service to end customers, leading to operational disruptions and security weaknesses.
- Identifying critical system profiles and making the business-critical information available can be chaotic. Transferring business-critical data, access permissions, and entitlements from one IAM system to another can be challenging, causing data migration errors or inconsistencies that can result in access issues, data loss, or unauthorized access.
- The merged IAM system should be compatible with existing infrastructure, applications, and technologies. Compatibility issues may arise due to differences in protocols, standards, or system architectures. Ensuring interoperability between systems is essential to avoid disruptions and maintain seamless operations.
How Can Users And “Privileged” Users Operate Seamlessly?
- Merging IAM systems involves addressing users’ and VIP users’ access rights and privileges, resulting in resistance, confusion, or decreased productivity. Awareness and clear communication can help reduce the noise in the helpdesk.
- Merging organizations often have different organizational cultures, work practices, and user expectations. These differences can impact the acceptance and adoption of the new IAM system. Effective change management strategies, including communication, collaboration, and involvement of key stakeholders, are essential to address cultural challenges and ensure successful integration.
How YASH Approach for IAM Impacts End User Experience
Ensuring customer satisfaction during an M&A isn’t just about improving their access experience; enabling the employees at the customer-facing touchpoints will deliver positive business results. Being able to offer IAM to offer more services to end customers can be a competitive market advantage.
Planning for IAM solution licenses and integrating business applications is essential, considering potential legacy applications requiring older versions of IAM solutions.
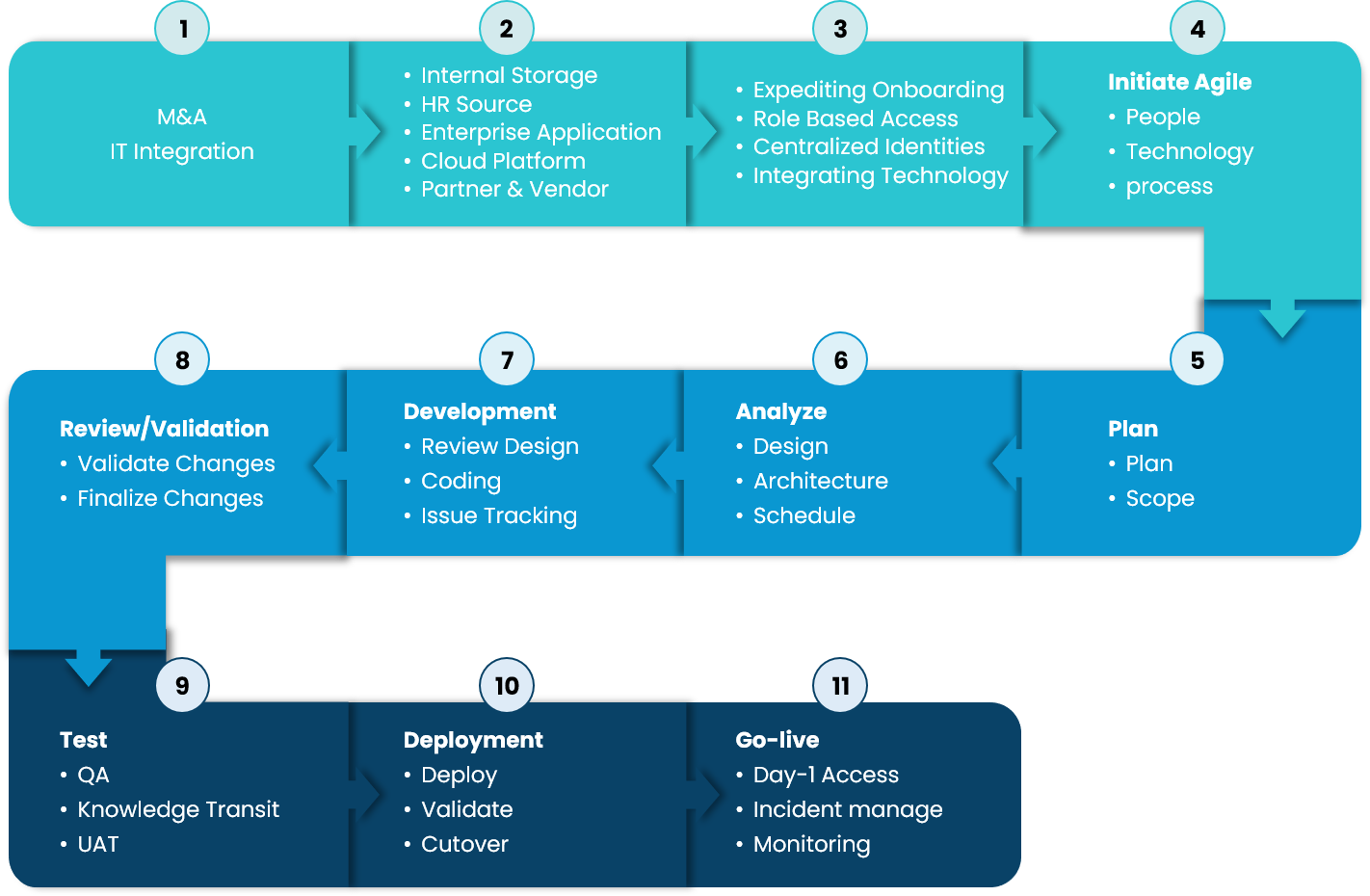
YASH’s M&A integration framework comprises risk management strategies, shadow repository features, etc. Our approach has helped customers to address crucial IT integration challenges post-M&A, allowing:
-
- Business-aligned approach for migrations
- Accelerating onboarding and access processes, workflows
- Seamlessly integrating systems and technologies
- Managing identities across directories
- Continual risk assessment and zero error migration policies
- Minimize service tickets and improve user CSAT
Addressing IAM Challenges During M&A:
- YASH takes a holistic approach to tackling the intricate challenges of Identity and Access Management (IAM) by recognizing the multidimensional nature of these technology challenges. Our M&A framework includes a comprehensive process considering various IAM integration facets.
- We worked with our customers to offer IAM in a Managed Service model. YASH understands the customer pain of managing the costs towards IAM implementation in the context of M&A. By opting for IAM as a managed service. We tap into dedicated professionals’ expertise to ensure a streamlined IAM process.
- The Managed Services approach frees up your internal resources, allowing businesses to concentrate on core business functions while entrusting IAM management to seasoned experts. We have also delivered a support desk to listen to end users and promptly address their issues.
- Establishing a forward-looking identity and access fabric is essential. Our M&A-specific architectural approach unifies diverse IAM elements into a cohesive and adaptable service structure. By creating a flexible fabric, we have enabled smooth business operations with enhanced security and allow sustenance in the post-M&A environment.
YASH M&A Identity and Access Management Programs:
The complexities (in M&A) of integrating various systems and user bases demand a strategic approach to ensure a seamless transition. IAM serves as the linchpin in addressing the intricate challenges that arise during M&A transactions. YASH’s M&A IAM programs provide a structured approach to expedite onboarding and access processes, a pivotal aspect in the post-M&A phase. Some of these include:
- Risk assessment and plan delivering cost-effective methodologies to the madness in M&A processes, including selecting IAM for critical systems, etc.
- Building interim vs. desired IAM state strategies
- Evaluate and define access roles before or during M&A, aligning them with user needs rather than titles for clear and predefined access policies.
- Streamline target access management through automated provisioning, ensuring efficient user lifecycle management during M&A.
- Centralize control over privileged access, restrict/ unauthorized definitions, and build/enforce least privilege principles for enhanced security in M&A.
- Perform regular reviews of access rights, applications, roles, and certifications to address unusual access patterns during M&A.
- Build User Behaviour Analytics (UBA) to see user behaviors in the new world and visualize insights into access risks, comprehensively analyzing relationships between identities, access, policies, and resources during M&A. This has helped our customers to refine the system access and define policies that promote superior end-customer service.
Mergers and acquisitions (M&A) can be complex and challenging, especially regarding security. The two companies involved may have different systems, policies, and procedures, making it difficult to integrate them securely. This is where identity and access management (IAM) can play a vital role. Involving IAM experts early in the M&A process can help ensure security is properly considered and implemented. By working with a trusted IAM partner like YASH, organizations can minimize business disruption and boost security services to their end customers.
Here are some additional tips for enhancing security in M&A with IAM:
- Use a centralized IAM solution to manage user identities and access across all systems.
- Implement strong passwords and multi-factor authentication.
- Monitor user activity for suspicious behavior.
- Keep IAM policies and procedures up to date.
By following these tips, organizations can help to protect their data and systems during M&A.
Click here to talk to our cybersecurity experts today, or write to us cybersecurity@yash.com
Senthilvel Kumar
Vice President – Cyber Security Services
Senthil is a cyber security Practice Head and VP at YASH offering advisory on cyber security solutions to CxO's, CISO, Board Level Executives for building a robust security modernization programme covering on-prem and Cloud.
Debashish Das
Solution Architect - Identity Access Management
Debashish Das is a solution architect with over 10 years of experience in Identity Access Management (IAM). He is an expert in using IAM & PAM tools, technologies, and platforms to help organizations achieve compliant and secure systems. Debashish has helped different industries and organizations achieve their IAM goals through mergers and acquisitions. He is a passionate advocate for security and privacy, and he is always looking for new ways to improve IAM systems and make them compliant and secure by design.