A Plain-English Guide for Security Professionals and Business Leaders
Insights from Gartner, SANS Institute, and Microsoft | 2025–2026
The Threat Landscape Has Changed — Have Your Defenses?
Many organizations are still trying to defend modern cyberattacks with tools built for an earlier era.
Traditional antivirus was designed to detect known threats. But today’s attacks are faster, stealthier, and increasingly AI-assisted. Ransomware can spread in minutes. Attackers use legitimate tools already present in the environment. Social engineering is more convincing than ever. And in many cases, there is no obvious “malware file” to catch.
This is where AI-powered Endpoint Detection and Response (AI-EDR) has become essential. Instead of only looking for known bad files, AI-EDR watches for suspicious behavior, identifies threats in real time, and helps stop attacks before they spread.
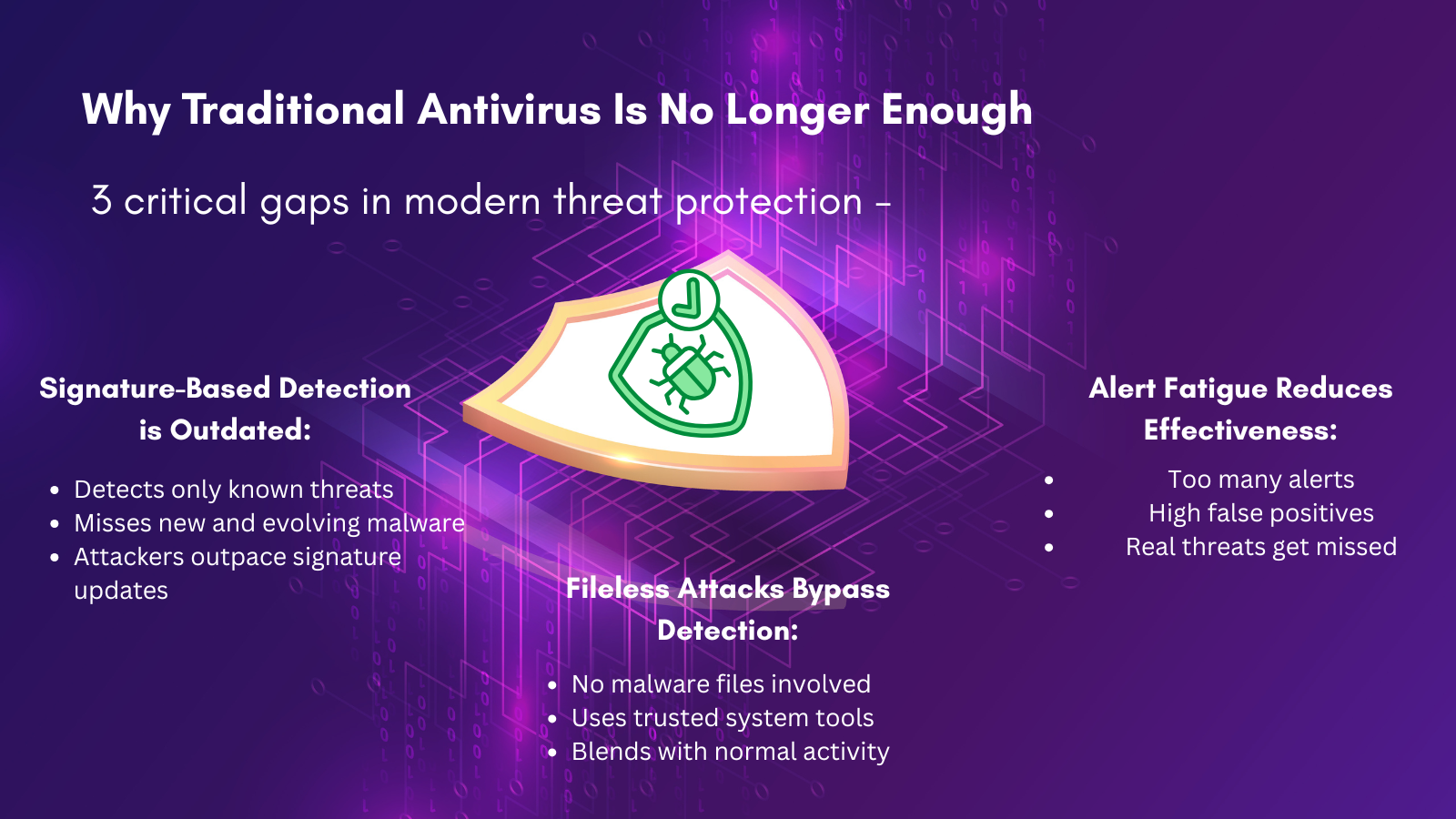
Part 1: Why Traditional Antivirus Is No Longer Enough
Traditional antivirus tools were built for a different era — one where threats evolved slowly and predictably.
Today’s threat landscape is faster, stealthier, and more complex.
From AI-generated malware to fileless attacks and alert overload, traditional approaches are no longer sufficient.
As the SANS Institute highlights, organizations are rapidly shifting toward behavior-based and AI-driven security models.
Part 2: What Is AI-Powered EDR and How Does It Work?
AI-powered EDR continuously monitors what is happening across endpoints — laptops, servers, desktops, and devices — and looks for signs of malicious behavior in real time.
- Real-Time Telemetry
AI-EDR collects endpoint activity such as:
- process execution
- file changes
- network connections
- user logins
- memory activity
This creates the visibility needed to spot attacks as they unfold.
- Behavioral Analytics
Instead of only asking, “Is this file known to be bad?” AI-EDR asks, “Does this behavior look suspicious?”
For example, if PowerShell suddenly starts reaching out to unknown external servers or modifying critical settings, AI models can flag that behavior even if no known malware signature exists.
- Machine Learning and Anomaly Detection
AI-powered EDR uses machine learning to recognize patterns linked to modern attacks. It can detect sequences of suspicious activity that, on their own, may look harmless — but together signal compromise.
- Automated Response
The real advantage is speed. AI-EDR can automatically:
- isolate compromised devices
- kill malicious processes
- block attacker activity
- contain threats before they spread
That machine-speed response is critical in ransomware and fast-moving attack scenarios.
- The AI Analyst
Modern platforms also help explain incidents. AI copilots and automated investigation tools can summarize alerts, recommend next steps, and reduce pressure on overburdened analysts.
This is helping modern SOCs move from manual firefighting to intelligent response.
Part 3: Real-World Impact — What the Numbers Say
Research cited by Gartner, Microsoft, and SANS consistently points to the same conclusion: modern endpoint security is increasingly defined by behavioral detection, automation, and AI-assisted investigation.
This matters because in cybersecurity, reducing response time by even 30–50% can mean the difference between a contained incident and a major breach.
Part 4: AI on Both Sides of the Battle
One of the biggest shifts in cybersecurity today is this: AI is helping both defenders and attackers.
Attackers are already using AI to:
- scale phishing campaigns
- create convincing social engineering lures
- mimic legitimate user behavior
- generate new malware variants faster
Now this changes the equation.
If attackers are moving faster with AI, defenders cannot rely only on static rules or manual review. Security teams need AI-powered detection and response to keep pace.
This is one reason why Gartner’s 2025 endpoint security research places such strong emphasis on AI-driven platforms, automation, and unified security operations.
Part 5: The Modern SOC — What AI-EDR Changes About Security Operations
AI-powered EDR is not just a better endpoint tool — it is changing how modern security teams operate.
From Reactive to Proactive
Traditional SOCs wait for alerts. AI-EDR helps teams become more proactive through:
- automated detection
- intelligent threat hunting
- faster investigation
- continuous monitoring
Reducing Analyst Burnout
Security teams are under pressure, and skilled analysts are hard to find. AI-EDR helps reduce repetitive work by handling triage, enrichment, and first-level investigation tasks.
AI Still Needs Human Judgment
AI improves scale and speed, but human expertise still matters. The best security operations combine:
- AI for volume and automation
- humans for judgment, strategy, and complex decisions
That is what SOC modernization increasingly looks like in 2026.
Part 6: Practical Takeaways — What Your Organization Should Do Now
If your organization is evaluating or improving endpoint security, here are the priorities that matter most:
- Assess your current endpoint coverage
Make sure EDR capabilities are actually deployed and fully configured. - Prioritize behavior-based detection
Look beyond signature coverage and focus on anomaly detection and automated response. - Integrate endpoint telemetry with SIEM/XDR
AI-EDR is most effective when connected to identity, cloud, email, and network signals. - Invest in threat hunting
Do not wait only for alerts — actively look for hidden threats. - Build AI governance into your security program
As AI adoption grows, security teams need visibility into how AI is being deployed and protected.

Part 7: Looking Ahead — Where AI-EDR Is Going
Endpoint security is evolving quickly, and AI is at the center of that shift.
Autonomous Security Operations
Leading platforms are moving toward more autonomous workflows, where AI handles much of the routine detection, investigation, and response.
Predictive Defense
The next frontier is not just stopping attacks in progress — it is predicting attacker movement and blocking likely paths before they are exploited.
Beyond the Endpoint
The future is broader than endpoint protection alone. Security is increasingly moving toward XDR-style visibility, where endpoint, identity, email, cloud, and network signals are connected into one intelligent defense model.
Conclusion: AI-EDR Is Not Optional — It Is the New Standard
The combination of AI-assisted attackers, fileless techniques, and the limits of traditional antivirus has made AI-powered EDR a baseline requirement for modern cyber defense.
The direction is clear. Research from Gartner, SANS, and Microsoft shows that endpoint security is moving decisively toward:
- behavioral AI
- automated response
- unified visibility
- SOC modernization
AI-powered EDR does not make cybersecurity simple. But it does give security teams the speed, scale, and intelligence they need to defend against threats that older tools were never designed to stop.
The question is no longer whether organizations need AI-powered endpoint security.
The real question is how quickly they can operationalize it effectively.
“Defender shifts security from reactive firefighting to proactive protection, embedding AI into the foundation of our protection solutions for instant detection, disruption, and containment — before threats escalate.”
Sources and Further Reading
The insights in this blog draw from the following primary sources published in 2025 and 2026:
- Gartner Magic Quadrant for Endpoint Protection Platforms, July 2025 (Evgeny Mirolyubov, Franz Hinner, Deepak Mishra)
- Gartner Market Guide for Endpoint Detection and Response Solutions, 2025
- SANS 2025 Detection Engineering Survey — Advancing Threat Detection: AI, Automation, and the Future of Cybersecurity (February 2025)
- SANS 2025 Threat Hunting Survey: Advancements in Threat Hunting Amid AI and Cloud Challenges (March 2025)
- SANS 2025 AI Survey (CISO Guide: AI’s Security Impact)
- SANS 2025 Detection and Response Survey Webcast — Understanding Blind Spots in Modern SOC Operations
- Microsoft Ignite 2025: What’s New in Microsoft Defender (November/December 2025)
- Microsoft Secure 2025: Introducing Security Copilot Agents and Autonomous Defense Capabilities (March 2025)
- Microsoft Digital Defense Report 2025
- Microsoft Behavioral Blocking and Containment — Microsoft Learn Documentation
- SentinelOne Singularity Platform — 2025 Gartner Magic Quadrant Recognition Blog (July 2025)
Palo Alto Networks Cortex XDR — 2025 Gartner Magic Quadrant Recognition Blog (July 2025)
Vikash Kumar
Sr. Manager - Cybersecurity
Vikash serves as a Senior Manager at YASH Technologies, where he drives service delivery for the NAM accounts and supports Endpoint Detection and Response (EDR) services across the organization’s portfolio.