Why Third-Party Risk Can No Longer Be Manual: Building an AI-Driven TPRM Program
Publish Date: February 26, 2026Third-party ecosystems are growing faster than most organizations can realistically govern them.
Cloud providers. SaaS platforms. Logistics partners. Payroll processors. IT contractors. Each one adds operational value. Each one also expands your risk surface.
Yet in many enterprises, Third-Party Risk Management (TPRM) still relies on annual questionnaires, spreadsheets, and email chains.
That approach might satisfy a compliance requirement.
It does not provide assurance.
In 2025, manual TPRM is no longer defensible.
The Reality: Your Risk Is Now Shared
Every vendor with access to your systems, data, or network extends your attack surface.
If a vendor:
- Suffers a ransomware incident
- Leaves critical systems unpatched
- Exposes credentials
- Onboards an insecure subcontractor
Your organization inherits that exposure.
Recent breach trends consistently show that third parties are common entry points for large-scale cyber incidents. At the same time, regulators increasingly expect demonstrable, ongoing vendor oversight — not static documentation gathered once a year.
Why Manual TPRM Is Breaking Down
1. Snapshots Create Blind Spots
Annual questionnaires capture a moment in time, not a living risk posture.
A vendor may attest to strong controls in January. By April, a critical vulnerability may be publicly disclosed, or a configuration may change. Manual programs rarely detect those shifts between review cycles.
Risk evolves continuously. Manual oversight does not.
2. Evidence Collection Drains Capacity
Collecting certifications, SOC reports, insurance policies, and penetration test summaries remains largely manual.
The result?
Expired documentation.
Inconsistent records.
Heavy administrative burden.
Highly skilled analysts spend time chasing paperwork instead of analyzing real risk signals.
3. Self-Reported Risk Is Not Verified Risk
Questionnaire-based scoring relies heavily on what vendors say about themselves.
Without independent validation, risk ratings reflect declarations — not observable exposure, vulnerability posture, or live threat intelligence.
There is often little correlation between a vendor’s self-assessed maturity and their real-world attack surface.
4. No Continuous Monitoring
Vendors change constantly. Infrastructure shifts. Incidents occur.
Manual programs typically learn about these changes only when vendors disclose them — or during the next scheduled review.
That creates long visibility gaps.
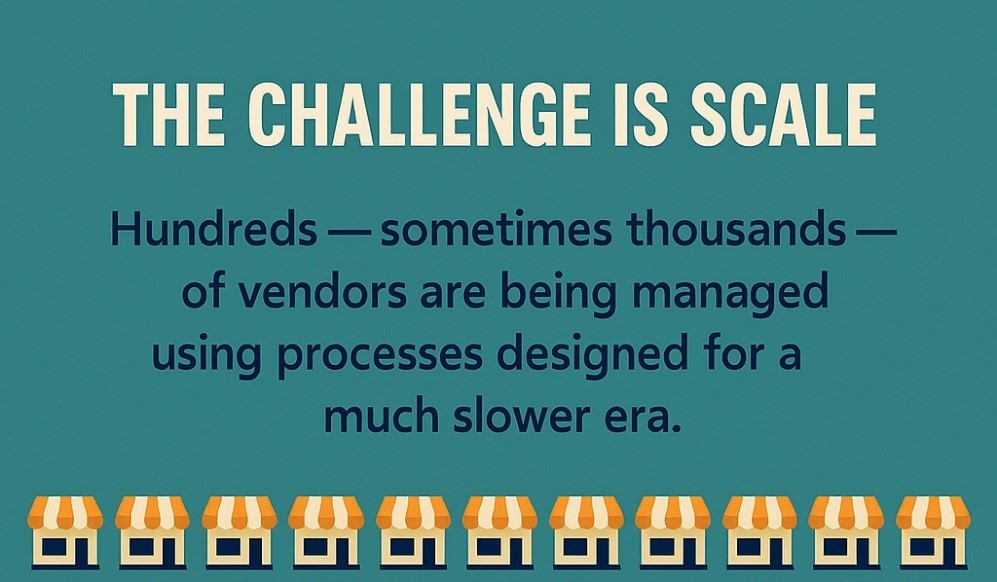
5. Scale Outpaces Human Capacity
Even well-resourced teams cannot deeply assess every vendor in a large portfolio.
Tier 1 vendors receive scrutiny.
Tier 2 and Tier 3 vendors often receive minimal review.
Yet history shows that less-scrutinized vendors frequently become entry points into larger enterprises.
What AI-Driven TPRM Changes
Artificial intelligence doesn’t replace human judgment.
It amplifies it.
AI enables speed, correlation, and continuous visibility that manual processes cannot achieve.
Continuous Vendor Monitoring
AI-powered TPRM platforms ingest live data sources, including:
- Public vulnerability disclosures
- Threat intelligence feeds
- Breach databases
- Dark web exposure indicators
- External attack surface analysis
If a vendor’s infrastructure communicates with malicious domains, alerts can trigger immediately. If a critical vulnerability affects their public-facing assets, visibility becomes near real-time.
This is the shift from reactive awareness to proactive oversight.
Intelligent Evidence & Workflow Automation
AI also streamlines documentation and workflow.
It can:
- Automate evidence requests
- Extract metadata from uploaded reports
- Track expiry dates
- Detect inconsistencies
- Trigger reassessments when thresholds are crossed
Risk teams move from administrative coordination to analytical focus.
Dynamic Risk Scoring
Instead of static questionnaire scores, AI enables multi-source risk modeling based on:
- Observed external exposure
- Vulnerability trends
- Incident history
- Business criticality
- Data sensitivity
Scores evolve as vendor posture changes, reflecting current risk rather than historical responses.
Event-Driven Reassessment
Traditional TPRM is calendar-driven. AI-driven TPRM is event-driven.
When a breach disclosure occurs or a vendor’s risk score declines materially, reassessment workflows trigger automatically.
Intervention happens in days — not months.
Enhanced Board Visibility
AI platforms generate structured dashboards that provide leadership with:
- Aggregate third-party risk posture
- High-risk vendor exposure
- Risk movement trends
- Compliance alignment status
The conversation shifts from “We completed annual reviews” to “Here is our real-time vendor risk landscape.”
That distinction matters at the board level.
Regulatory Expectations Are Rising
Modern frameworks increasingly require active oversight, including:
- ISO 27001 supplier security controls
- SOC 2 vendor monitoring requirements
- GDPR processor accountability
- DORA continuous ICT third-party oversight
- NIS2 supplier risk obligations
Manual programs struggle to demonstrate continuous monitoring.
AI-driven TPRM strengthens defensibility through automated audit trails, structured reassessment logs, and real-time monitoring records.
Addressing Common Concerns
“We only have a limited number of critical vendors.”
Even small portfolios evolve quickly. Continuous visibility reduces uncertainty.
“We already use a GRC platform.”
GRC systems manage workflows. AI-driven TPRM enriches them with live external intelligence. They complement each other.
“The investment may not justify the cost.”
The financial and reputational impact of a single vendor-driven breach often exceeds the cost of scalable monitoring.
The Strategic Imperative
Third-party risk is no longer periodic.
It is continuous.
Spreadsheets and annual questionnaires cannot keep pace with modern vendor ecosystems or regulatory demands.
AI-driven TPRM enables:
- Continuous risk visibility
- Event-driven reassessment
- Reduced administrative burden
- Scalable oversight
- Stronger compliance defensibility
The organizations best positioned to manage vendor risk are not those with the largest teams — but those leveraging intelligent platforms to maintain real-time awareness.
AI has already begun redefining TPRM.
The only question now is whether organizations adopt continuous intelligence before — or after — their next third-party incident.
Shivaram Jeyasekaran
Director – Cybersecurity Services, YASH Technologies
A distinguished cybersecurity leader with over 23 years of experience transforming enterprise security landscapes across global organizations. He is recognized for architecting and scaling robust cybersecurity programs that align with business objectives while maintaining cutting-edge defense capabilities. Shivaram has spearheaded numerous large-scale cybersecurity consulting engagements in his illustrious career, helping organizations navigate complex security challenges while balancing innovation with risk management. His approach combines strategic vision with practical implementation, ensuring organizations stay resilient in the face of evolving cyber threats.