Turning Data Security Assessment into Measurable Outcomes in the AI Driven Breach Era
Publish Date: March 6, 2026For today’s CIO and CISO, the business problem is no longer “Are we secure?” It is far more direct:
Can we quantify our data risk in a way that reduces breach impact, regulatory exposure, and AI-driven uncertainty?
Can we demonstrate, with measurable evidence, that our data exposure is decreasing — even as AI accelerates both innovation and attack velocity?
At the same time, generative AI has reduced the technical barrier for attackers. AI-assisted reconnaissance can enumerate exposed storage, identify sensitive patterns, correlate leaked credentials, and simulate privilege escalation paths in minutes. What previously required skilled manual effort is now automated.
“According to the IBM Cost of a Data Breach Report, the global average cost of a breach has surpassed $4 million, with detection and containment often exceeding 200 days.
In cloud-heavy and highly regulated environments, impact escalates significantly due to scale and regulatory penalties.
Here’s the Real Problem Leaders Need to Solve
Most enterprises have invested in encryption, DLP, IAM, and cloud security tooling. Yet breaches continue. The failure is rarely the absence of tools — it is the absence of integrated, measurable visibility.
Cloud adoption, SaaS sprawl, and AI experimentation have multiplied data copies across repositories. Sensitive datasets now exist in object storage, analytics environments, collaboration platforms, AI training pipelines, and third-party integrations.
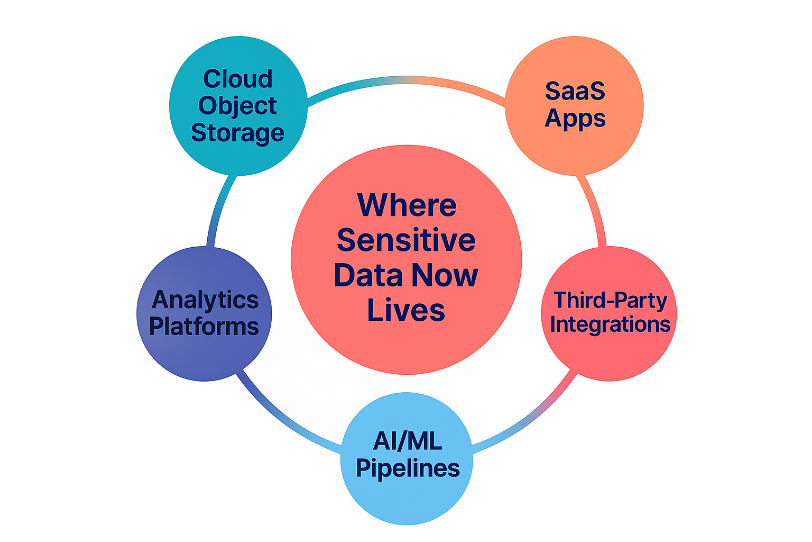
When CIOs are asked how much regulated or confidential data exists across these environments — and who can effectively access it — answers are often approximate.
Why Checklist Assessments Fail Executive Expectations
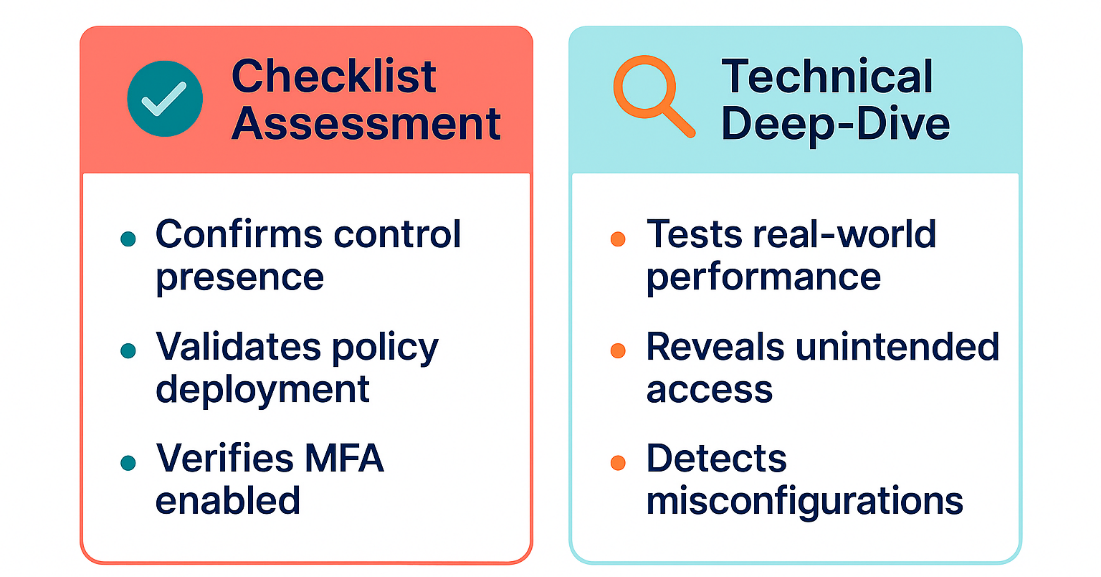
Traditional assessments still matter — they verify that organizations have the right policies and controls in place. However, they rarely show whether those controls are actually working. A checklist can confirm that encryption is enabled or that DLP and MFA are deployed, but it cannot reveal if sensitive datasets remain overexposed, if inherited permissions are granting unintended access, or if cloud and SaaS configurations are silently expanding breach impact.
This is where a technical deep‑dive assessment becomes essential. Instead of asking, “Do we have the control?” it answers, “Is the control effective in real operating conditions?
A technical assessment evaluates how sensitive data is accessed across cloud, SaaS, and analytics environments. It identifies dormant privileged accounts that still retain access to regulated data, detects misconfigurations that may expose storage externally, validates whether encryption is applied consistently across platforms, and uncovers whether AI training datasets are aggregating regulated or confidential information without governance oversight.
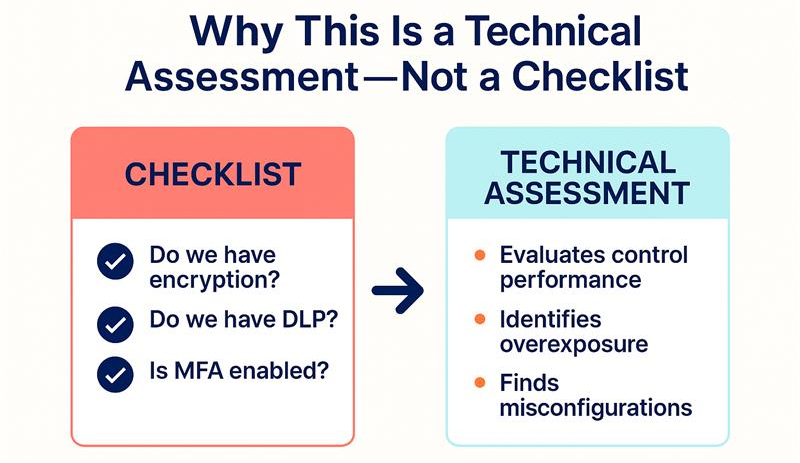
In simple terms, a checklist tells leadership that controls exist — a technical assessment shows the true level of exposure behind those controls. For CISOs, this difference determines regulatory defensibility. For CIOs, it determines whether the organization’s architecture is resilient, not just documented.
Why Data Security Posture Assessment Is Now a Strategic Imperative
The AI-driven breach era introduces three structural changes:
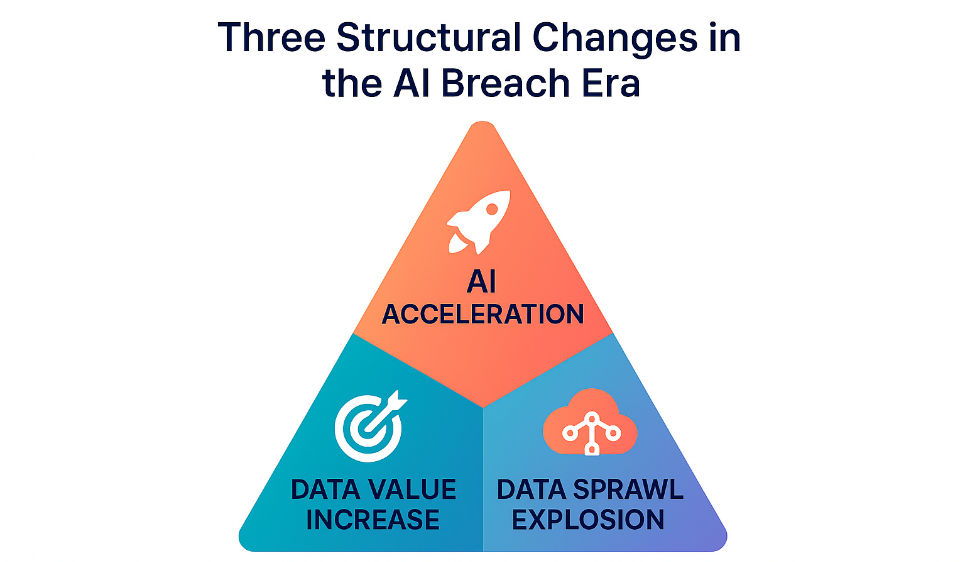
- Data is the primary target: Cloud object storage, SaaS repositories, analytics platforms, and AI training datasets are high-value assets. Infrastructure compromise is merely a pathway.
- AI enhances attacker efficiency: Automated enumeration of exposed storage, excessive permissions, API pathways, and SaaS integrations reduces the time between initial access and data exfiltration.
- Data sprawl has outpaced governance: Multi-cloud adoption, shadow SaaS usage, DevOps pipelines, and AI experimentation have created uncontrolled data replication.
A Data Security Posture Assessment provides this integrated visibility. For the CIO, it establishes architectural clarity. For the CISO, it quantifies exposure and aligns it to business risk.
The Business Impact for CIO and CISO
A measurable Data Security Posture Assessment solves tangible executive challenges:
- It reduces regulatory exposure by demonstrating effective control validation rather than policy existence.
- It strengthens cyber insurance negotiations through quantified risk improvement evidence.
- It enables responsible AI adoption by embedding data governance into innovation cycles.
- It provides the board with trend-based risk indicators instead of static compliance artifacts.
- It aligns data architecture with enterprise risk appetite.
Most critically, it transforms data security from an annual audit event into a continuous risk optimization program.
And in the AI era, unmanaged data risk is no longer a technical issue — it is a board-level business liability.
Shivendra Sharma
Technical Architect - Cybersecurity
Shivendra is a cybersecurity solution architect at YASH, focusing on building security strategies and executing solutions for security leaders that connect with their business objectives.