Don’t Consider Audit Findings As Failures — They’re Blueprints for Your Next-Generation Data Security Architecture
Publish Date: March 6, 2026For CIOs and CISOs, the uncomfortable pattern is familiar: excessive privileged access, inconsistent encryption, unclassified sensitive data, limited visibility into data movement. The findings are closed, evidence is submitted, and the organization moves forward—until the next cycle reveals variations of the same or other weaknesses.
The implication is clear: organizations are not primarily losing control due to unknown threats. They are losing control because architectural maturity has not kept pace with data growth.
Here is the strategic reality: audit findings are not failures. They are architectural feedback.
Core Problem is “Audit-Driven Remediation” – time is to change the perception and Reframe Audit Findings as Design Inputs
Most enterprises operate in a cyclical control model. Audits identify gaps. Teams remediate tactically. Documentation improves. Risk appears reduced. But the underlying environment continues to evolve—new cloud workloads, SaaS platforms, AI pipelines, third-party integrations.
Controls validated annually cannot govern environments that change daily. This mismatch explains why findings recur. The issue is not negligence. It is structural misalignment between static validation and dynamic risk.
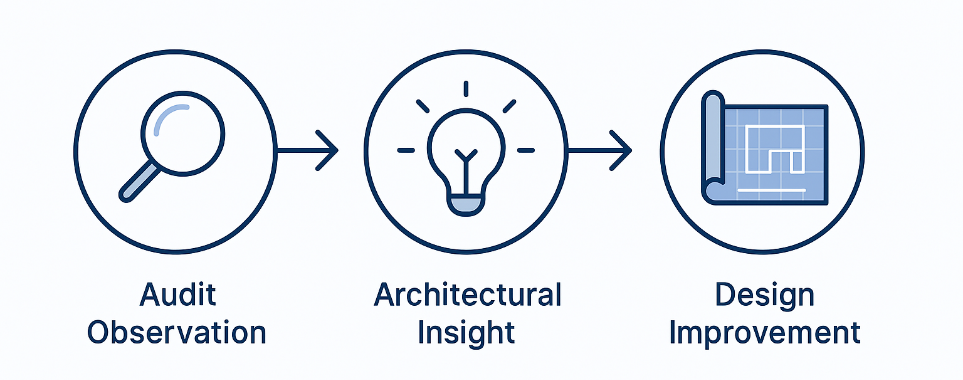
Forward-looking organizations treat audit observations as telemetry for redesign. Each finding signals where the architecture lacks continuous validation.
- If sensitive data is repeatedly discovered in unmanaged repositories, the enterprise likely lacks automated discovery and classification embedded into its data lifecycle.
- If excessive privileges reappear, entitlement governance is static in a dynamic ecosystem.
- If encryption coverage is inconsistent, protection controls are not integrated into provisioning workflows.
These are not operational oversights—they are architectural design opportunities.
Frameworks such as the NIST Cybersecurity Framework from the National Institute of Standards and Technology provide lifecycle guidance—Identify, Protect, Detect, Respond, Recover. The challenge is not alignment in principle, but execution in continuity.
Designing a Modern Data Security Architecture
A modern data security architecture must be engineered around three realities: data is fluid, access is dynamic, and threats are adaptive.
- First, visibility must be continuous. Automated discovery and classification across structured and unstructured data environments ensure that sensitive data sprawl is identified in real time, not rediscovered during audits.
- Second, access governance must become dynamic. Privileges should be evaluated contextually and continuously, reducing entitlement accumulation and shrinking the attack surface over time.
- Third, protection and detection must be data-centric. Encryption posture, behavioral monitoring, and anomaly detection should operate directly around sensitive datasets—not merely at the network edge.
When these capabilities operate as an integrated system, audit findings decline organically because systemic weaknesses are engineered out.
For CIOs and CISO the Strategic Opportunity is to shift From Compliance Metrics to Data security posture Risk Trajectory
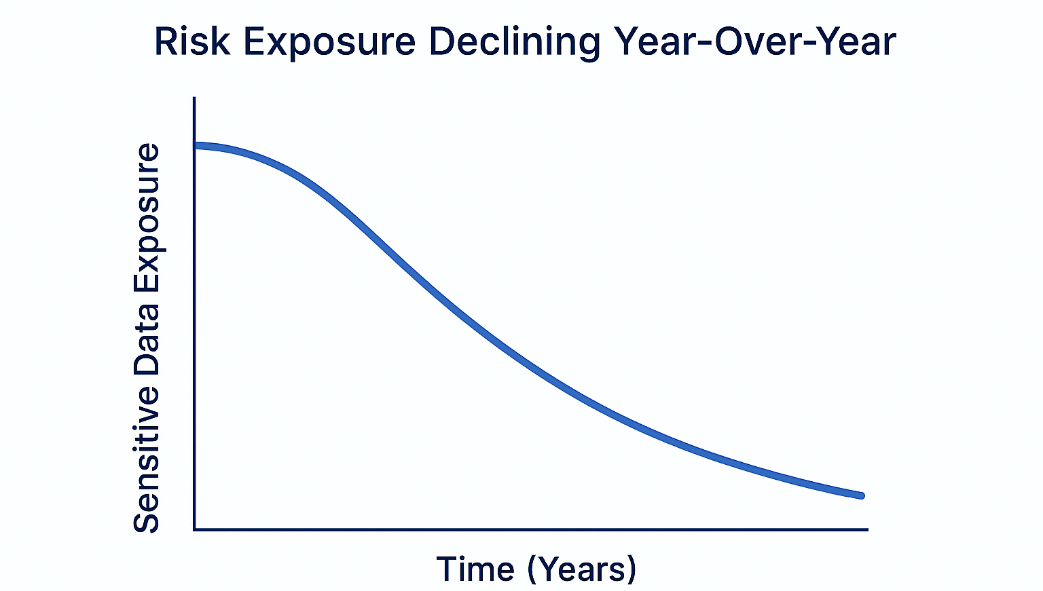
Instead of highlighting the percentage of findings closed, security leaders should demonstrate measurable reduction in sensitive data exposure, contraction in high-risk privileges, and improved time to detect anomalous access.
Boards understand trajectory. They understand risk reduction curves. They value evidence that exposure is declining year over year.
Audit fatigue is common. But audit insight is invaluable.
For CIOs and CISOs, the opportunity is to transform audit observations from recurring disruptions into stepping stones for architectural modernization. When findings are treated as structured intelligence rather than compliance setbacks, they become catalysts for continuous protection.
Shivendra Sharma
Technical Architect - Cybersecurity
Shivendra is a cybersecurity solution architect at YASH, focusing on building security strategies and executing solutions for security leaders that connect with their business objectives.